Linux Porter Discovered M1 Covert Channel Flaw Named ‘M1RACLES’
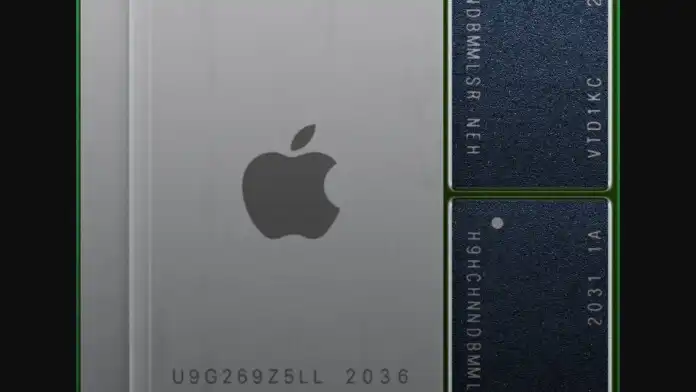
Hector Martin, a hacker who is porting Linux to Apple Silicon Macs through Asahi Linux, has discovered a novel covert channel vulnerability on the M1 chip, calling it ‘M1RACLES’ and tracked as CVE-2021-30747. The flaw lies in the design of the chip itself, allowing any two applications running under an OS to covertly exchange data between them without using memory, sockets, files, or any other features that are meant to be used for data exchange. "While this shouldn’t be allowed as it bypasses OS security layers, it is nothing to worry about in practice."
This problem applies even if the two intercommunicating processes belong to different users and run on different privilege levels.
Because this vulnerability is bound to the chip itself, it doesn’t matter if the user is running macOS, or Linux, or OpenBSD, or anything else on it. Every M1 device is affected by M1RACLES, and the only mitigation that can address the issue is to run the entire OS as a virtual machine. Obviously, this would impact the performance greatly, but would it be worth it? Is M1RACLES that serious to call for such a drastic measure?






![Multiple Chromium DoS, Info Disclosure Vulns Fixed [Updated] 23.Tablet Connections Esm W300](/images/articles/900x500/23.Tablet_Connections.jpg#joomlaImage://local-images/articles/900x500/23.Tablet_Connections-esm-w300.jpg?width=900&height=500)
















