Distro Advisories For This Week
What Are You Looking To Secure Today?
Join Our Community
Join our community and get the latest security insights delivered to you.
Featured Articles
Compromised VS Code Extension Puts Linux Development Pipelines at Risk
The compromise of Nx Console shows how much infrastructure now sits behind a single developer...
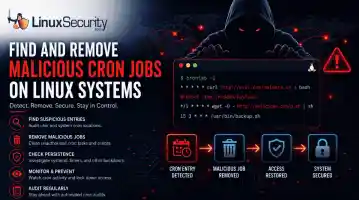
Linux Persistence Hunting: The 5 Techniques Security Teams Miss Most
You remove the malware. You rotate the compromised credentials. You patch the original...

Get expert insights in the realm of Linux Security
Subscribe to Linux Security Newsletters
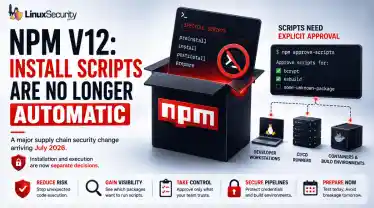
Red Hat npm Package Compromise Highlights a Growing Supply Chain Problem
Researchers investigating a campaign now tracked as Miasma found that more than 30 packages in Red...
Why Linux Rootkits Still Matter in Cloud and VMware Environments
Linux rootkits are old, but they never really disappeared. They just stopped attracting the same...
SSH Key Sprawl on Linux Unmanaged Access Threats and Cleanup Guide
A production Linux server gets rebuilt from an old image. A contractor leaves. A CI/CD job is...