Enhance Your Cybersecurity: Open-Source SAST and DAST Tools Explained

As open-source software becomes increasingly common in the infrastructure of businesses, it is essential to ensure the security of the software being relied upon. An increasingly popular cyber security solution is open-source SAST (Static Application Security Testing) and DAST (Dynamic Analysis Security Testing) security scanning, which give IT technicians and developers the ability to access the code of a certain piece of software to remove threats or improve the strength of its security.
Software scanning tools allow developers and users to scan the code of the programs they are using to check for security flaws. The two types of security tools, SAST and DAST, each have their strengths and weaknesses.
Running these tools (and your wider organizational systems) through an open-source operating system like Linux will provide you with additional security and peace of mind and increase control over your hardware infrastructure.
This is what you need to know about SAST and DAST on Linux and why it is important for your organization.
What Is Open Source Security?
Open-source is software that is accessible to outside users, who can change or share the source code at will. The source code, which open source refers to, is what can be used by developers or technicians to modify the nature of the software. This is used to improve performance, eliminate any technical gremlins, or bolster security. 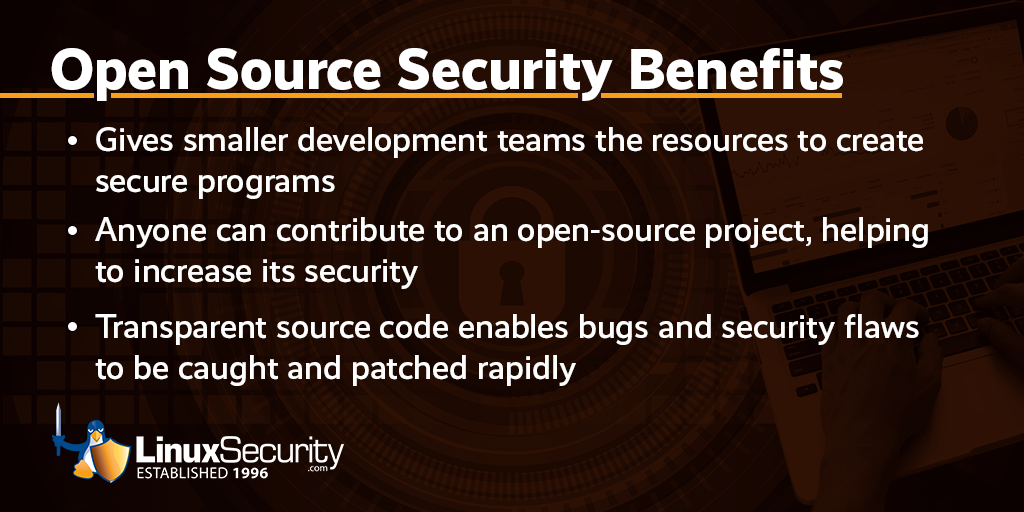
Naturally, open-source security allows you to be incredibly flexible with your security processes because you can immediately dive into the software and fix any issues. There is no need to wait for a software upgrade, call out a specialist, or leave yourself with lasting software problems at the whim of the proprietary software vendor that could damage your organization’s health and reputation.
Given the relentless demand for the latest software and technology solutions within businesses today, it is little surprise that open-source security processes are an increasingly prevalent means of tackling security problems.
Using the increasingly popular open-source Linux operating system offers additional security benefits due to its modular construction. This limits user access to applications and separates them from each other, meaning that if there were a cyber-attack, less damage would be done in a single breach.
Despite the benefits associated with open-source development discussed above, not every open-source security tool is equal, and there are a few different approaches to consider. This includes SAST and DAST tools, which we will cover in more depth below.
What Are SAST and DAST Tools?
Ultimately, SAST and DAST tools have the same goal- to improve the security of code within software. However, they take different approaches to solving this problem, which is important to note if you consider utilizing them.
What Types of Vulnerabilities can SAST Tools be Used to Find?
Firstly, SAST tools are used to examine software source code, which is still under development and not out on the open market. SAST tools can be of great assistance if you are trying to identify and fix bugs during the development phase of a piece of software or technology.
SAST tools work by analyzing code to look for vulnerabilities. They use the white box testing methodology, meaning the program is never actually run and is “tested” only on a logical level. By scanning the code, SAST tools can identify vulnerabilities such as:
- weak random number generation
- SQL injection
- cross-site scripting
- buffer overflows
Since SAST tools are usually used earlier in development, they can prevent the need to pull a piece of software later in the development cycle, which could cost a lot of time, money, and even reputational damage.
To further improve the efficiency of the software development process, you can add a SAST tool to an integrated development environment (IDE). Essentially, this alerts the development team of any technical glitches or software vulnerabilities as they work, speeding up the software creation process and minimizing the chance of errors.
What Types of Vulnerabilities can DAST Tools be Used to Find?
Conversely, a DAST tool is designed for use after a piece of software has already been completed. Unlike a SAST tool, a DAST tool does not focus on troubleshooting issues within the code. Instead, it attacks a system from the outside inwards, hacking the program using a variety of approaches - including through exposed HTML and HTTP.
Unlike SAST tools, DAST tools use a black box approach, meaning that the program is only tested from the outside without any knowledge of the inner workings, the way a hacker would likely attack it.
DAST tools are useful for finding:
- configuration problems
- issues with error handling
- input and output issues
Unlike SAST tools, DAST tools can not tell you from where in the code an error originates–it is by design as blind as a real user of the software would be.
A DAST tool is particularly useful if you have an existing system or piece of software that is likely to suffer from a certain cyber-attack. For example, if your organization operates an online retail store, then there are certain attacks you should be vigilant of. A DAST tool can be programmed to run a simulation of these hacks to expose any potential weaknesses within your infrastructure.
There is a tendency for businesses to focus on deploying either a SAST tool or a DAST tool, focusing on one as though it is better than the other. This is rarely the case because they fulfill different roles within your cyber security processes.
By using both tools, you safeguard yourself both at the software development and deployment phases.
Which Open-Source Security SAST and DAST Tools are Available?
There are various strong open-source security tools available, and choosing between them can be difficult.
Here are a few options to consider:
Zed Attack Proxy (ZAP): ZAP is a DAST tool available on Windows, Mac, and Linux that is designed primarily for testing web applications by using penetration testing. ZAP is a popular tool that is used by dozens of other services and has a beginner-friendly user interface.
GoLismero: GoLismero is another DAST tool and is available on Windows, Mac, BSD, and Linux. GoLismero is a bit less beginner friendly than ZAP, as it does not have a UI–it is installed and run solely via the command line. However, it is very robust as it consolidates the results of security frameworks including sqlmap, xsser, openvas, dnsrecon, and theharvester, and has several output options.
SonarQube Downloads: SonarQube is an SAST tool that can analyze 17 different languages including Java, Javascript, Python, HTML, and CSS. It also has a dynamic UI, a community forum, and thorough documentation. There are several expanded versions of SonarQube with more features and support for additional programming languages, but only the “Community Edition” is free and open-source.
w3af: w3af is a DAST tool designed primarily to test web applications. It is a framework specifically made to be easy to extend and incorporate into other projects. w3af can be downloaded on Linux, Mac, and BSD (it is also possible to run on Windows, but it is not officially supported or tested.)
What Are the Top Five Things I Should Look for in an Open-Source Security Scanning Tool?
With so many software scanning tools available, it can be helpful to narrow your focus when deciding what tools to use. Tips for choosing the right scanning tool include:
Easiness to Use (Especially if You’re a Beginner)
Not all software scanning tools are beginner friendly. Some tools, like the aforementioned GoLismero, can only be run or even installed using the command line. On the other hand, tools like ZAP and SonarQube are designed to be easier to use thanks to their detailed user interfaces, making them a good starting point.
What Programming Languages It Can Check
Not all tools are made for checking all types of programs. While some tools, like SonarQube, can check most types of code, tools like ZAP and w3af are made for testing certain types of programs, like web applications.
Limited False Positives
Software scanning tools sometimes make mistakes by flagging safe code as dangerous. Attempting to fix these nonexistent flaws can lead to wasting time by rewriting code for no reason, so it is important to look for scanning tools that have as few false positives as possible.
What Flaws It Can Find (Don’t Rely on Just SAST or DAST)
No one software can find every exploit. Because SAST and DAST tools use fundamentally different methodologies to find flaws and are meant to be used in different stages of development, they should ideally both be used in order to help find more types of errors and bugs.
Active Support, Updates, and Community (You Don’t Want a Tool that Can’t Find New Vulnerabilities)
When using any open-source software or tool, it is important to check that it is up to date and frequently updated since out-of-date code can be a security risk. Ensuring that the tools you are using are up-to-date is especially important with a security tool like software scanners so that they can find the latest exploits.
What Are Some Strengths and Weaknesses of Open-Source Testing Tools?
There are many strengths and weaknesses to be aware of when considering the use of open-source testing tools and open-source technology in general.
To start with the advantages, open-source testing tools can save your organization substantial money. When you have an open-source variant of a software solution, you can make changes yourself, adapt the software to your specific needs, and even operate without a license, all of which cuts a lot of unnecessary costs.
Furthermore, you will (hopefully) be able to identify problems within the system before they cause any significant damage. This could save your organization a substantial amount in damages, potential losses (both data losses and financial losses), and reputational damage.
Another key advantage of open-source testing tools is increased agility. When you can dive into open-source code at any time, fixing issues and improving performance are made far more efficient. Technically, anyone can work on the software, which eliminates potential delays in waiting for system updates or a professional fix.
When you are growing an organization quickly, delays in software updates or bug fixes can stop your progress overnight, so having user-focused testing tools allow you to constantly build upon your base layer solutions.
Know that Open-Source Tools Are Not Perfect
While open-source tools can provide many advantages, they are not perfect. Commercial tools often have more features. For example, as mentioned before, the paid, closed-source versions of SonarQube offer significantly more features and compatibility with more programming languages. The open-source version is more of a “try before you buy” where features are intentionally limited in an effort to draw clients to their subscription model; it’s not necessarily a limitation of open source itself.
However, many open-source scanning tools have large user bases with lots of community support, meaning that bugs can be fixed just as quickly, if not faster, as a proprietary closed-source software. Ultimately, it is up to developers to weigh the pros and cons of open-source tools against the needs of their projects.
Final Thoughts on DAST vs. SAST: Which One Is Better?
While SAST and DAST are both useful for testing the security of programs, they use fundamentally different methods for finding exploits. SAST programs analyze the code itself; while an error checker that analyzes code sounds more thorough, not all programming errors can be found in code. The fact that SAST never executes the program means that it can not find runtime errors or exploits that can be taken advantage of by a user. While DAST never looks at the code of the program it is testing, it is able to find runtime issues by executing the program.
It is unfair to say that either SAST or DAST is better–they both serve different purposes. Since SAST analyzes code, it is usually used earlier in development to assist with programming. On the other hand, DAST is usually used after the programming is finished as a way of finding exploits in the complete software. Both tools should be used hand in hand for ideal error prevention, and a best-practice security strategy should incorporate both SAST and DAST tools in its software development cycle.

