Guide to IT Security Audits

Protecting a business’ online assets has become difficult due to modern information storing and sharing methods. Sensitive intel is at risk more frequently online, so companies need to utilize thorough IT security audits to verify the safety of their information.
An IT security audit examines an organization’s safety practices, observing how they protect information from internal and external threats and determining data and network security issues in distribution. Cloud security audits can help identify common cyber risks and network security threats, which can be remedied to protect a company’s products and services. This article will discuss what you need to know about IT security audits, their importance, and how they help improve security posture against cybersecurity vulnerabilities.
What Network Security Issues Can Be Discovered Through IT Security Audits?
Information Risk
Organizations should protect their customers from data loss, theft, and misuse by utilizing penetration testing, a popular method for protection mentioned in information security news.
Network & Communications Risk
An organization should verify that data is transmitted securely through network infrastructure, preventing internal and external intruders from interfering with traffic to access sensitive information.
Mobile Device & Data Loss Risk
Organizations must take precautions when securing user-owned devices that utilize the company’s network, as crucial information is stored on external sources. When companies have a “Bring Your Own Device Service,” this becomes a problem.
An IT security audit involves penetration testing to check if a business's IT system is secure or carries multiple cybersecurity vulnerabilities. It shows an organization’s level of preparedness in dealing with various data and network security threats, providing a clear picture of how safe an institution is if facing such problems.
What Are the Benefits of Conducting IT Cloud Security Audits?
By conducting an IT security audit, you can quickly identify cybersecurity vulnerabilities in your organization that should be enhanced to protect against cybercrime and improve security posture.
Key benefits include:
- Provides detailed reporting about prevailing data and network security issues
- Helps to understand organizational policies & procedures
- Advises on technologies to be used for practical cybersecurity projects
- Identifies gaps between the current and desired states of IT security
- Offers knowledge about the best possible ways to address identified security gaps
IT Security Audits Vs. Other Frameworks
Frameworks other than IT security audits tend to examine organization controls without ever testing them, forcing companies to rely on previous cloud security audits to determine what changes need to be made. Even worse, such cloud security frameworks only address the required fixes.
IT security audits are more effective as they consider the latest risks and how to protect your company’s system from data and network security threats, patching cybersecurity vulnerabilities at the source.
Who conducts an IT security audit?
Internal staff members, third-party cybersecurity companies with certified ethical hackers, or outside consultants who use various methodologies and network security toolkits can perform IT security audits. Your business size plays a part in who is best to utilize in a cloud security audit, so just make sure you check their eligibility to execute such services, whether CISA, CISSP, or other certifications.
Why is an IT security audit important for your business?
If your business operates online and exchanges sensitive information, regular audits, whether quarterly or yearly, are effective in helping your organization determine the level of cybersecurity vulnerabilities you have within your company. This will allow you to take the correct steps to prevent future data and network security issues.
Which IT Assets are Involved in an IT Security Audit?
There are various components of a business being audited during this process:
- Endpoints: This refers to any device that enables access to your network or stores essential information, such as laptops, notebooks, smartphones, tablets, and more.
- Internet-connected devices: This means any hardware with an internet connection, including webcams, routers, printers, etc.
- Communication channels: Important communication channels used in your business, like FTP servers and SSH services, are usually scanned.
- Networks: Your organization's Local Area Network (LAN) is also checked.
- Data: Data within your company's infrastructure, whether physical files or virtual databases, is a crucial component examined during an audit.
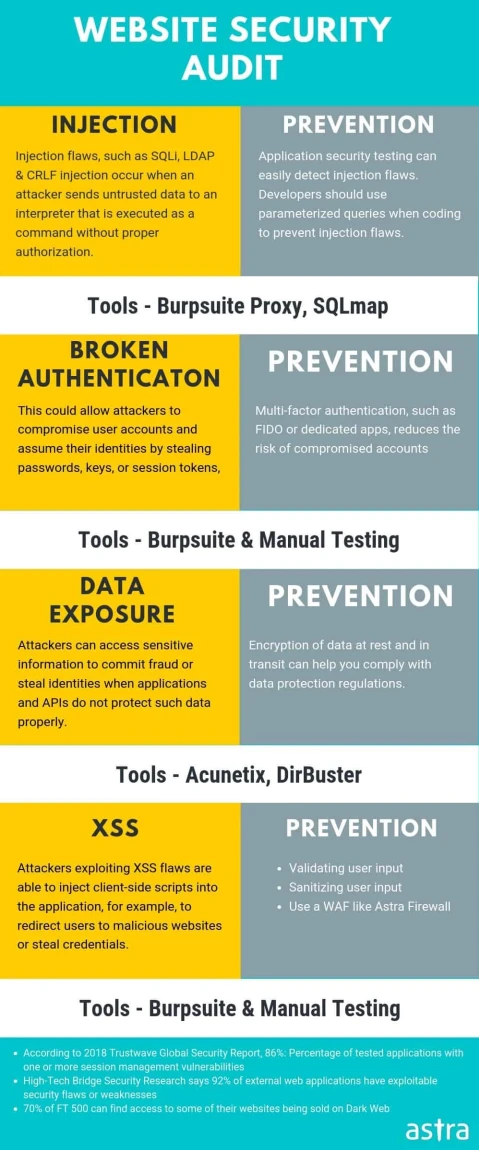
- Applications: A couple of the most critical applications in your organization's IT system include databases, accounting software, CRMs, and email services. You can check this guide for web application security vulnerability testing.
An IT security audit helps organizations determine their company's most targeted assets to protect them from malware penetration and exploitation, data loss, Denial of Service (DDoS) Attacks, and data and network security threats.
How Do I Conduct an IT Security Audit?
 Here are some guidelines you can utilize to help you perform an IT security audit:
Here are some guidelines you can utilize to help you perform an IT security audit:
Step 1: Define your objectives, including goals, time frame, etc.
Step 2: Understand your organization's existing policies and procedures so that new changes can be suggested accordingly.
Step 3: Evaluate the selected network security toolkits and technologies used in your business so that you can enhance and improve your security posture.
Step 4: Set up a proper change management structure to protect your system from unauthorized changes.
Step 5: Identify & prioritize data and network security issues so you can create mitigation plans to eliminate such cybersecurity vulnerabilities as soon as possible.
Step 6: Proceed with a risk assessment process to discover your business's existing data, network security threats, and web application security vulnerabilities.
Step 7: Check how efficient your company's security is compared to other organizations in your industry using benchmarking tests.
What Techniques Can I Use to Conduct an IT Security Audit?
There are three main types of cloud security audits you can use:
1. Internal Audits: Studies found that 60-80% of staff members have access to sensitive information, making a company vulnerable to internal attacks should information not be appropriately managed & secured. Internal audits are essential to execute so you can identify data and network security issues within your business and find affordable solutions.
2. Management System Audits: These are generally conducted for management purposes so managers can compare their organization's performance to similar organizations. These audits can be performed manually or with the help of automated network security toolkits and technologies.
3. External Audits: Banking, Financial Services, and Insurance (BFSI) companies can hire third-party cybersecurity firms to conduct these audits since they have sound knowledge regarding cybersecurity vulnerabilities. Therefore, firms can inform you of data and network security threats that must be handled within an organization.
These three types of audits are recommended to be utilized in any business to determine any risks that could be mitigated before attacks on network security.
How Can Companies Benefit from an IT Security Audit?
Organizations can use cloud security audits to help save time & money, promote threat awareness, help identify cybersecurity vulnerabilities, provide better protection against data and network security threats, reduce unauthorized access, and prevent information loss.
How Do IT Security Audits Help Secure a Business?
IT security audits can identify loopholes and improve security posture daily.
For example, if an online retail company utilized an external cybersecurity firm to conduct an IT security audit, the company could find out about data and network security issues that were impacting the system's overall functionality. Fixing these cybersecurity vulnerabilities helped the business and prevented customer data from being compromised.
This example highlights the value of using cloud security audits to prevent damage to a company’s reputation and income. If you want to protect your business from unwanted circumstances, investing in audits is always better.
Not only can IT security audits help companies and industries save money and effort, but they also provide companies with better protection against data and network security threats, saving money and helping businesses to run smoothly online.
How Do IT Security Audits Work?
An IT security audit is an assessment of the IT environment for any organization so that they can identify various data and network security issues or cybersecurity vulnerabilities within them. Here are the five main phases utilized during an IT security audit:
1) Planning & Preparation: You must first consider the best audit for your company before starting the actual process. This could be deciding between penetration testing and cybersecurity vulnerability assessments. Some audits need lots of preparation for a more successful scan for mitigation solutions.
2) Scope Determination: Auditors find all areas that need to be checked during the effective IT security audit to cover everything within the allotted time frame. This maintains the boundaries of a test while ensuring that all data and network security issues are identified.
3) Collection & Analysis of Evidence: During an assessment, evidence must be collected to see the severity of the cybersecurity vulnerabilities.
4) Reporting: Auditors will report the identified data and network security issues once enough evidence proves the problem exists.
5) Remediation: Companies will fix discovered cybersecurity vulnerabilities before anyone takes advantage of them and damages their data and network security.
What Tools Should I Use During an IT Security Audit?
 Tools you should use during an IT security audit include:
Tools you should use during an IT security audit include:
- Vulnerability Scanner: Following an audit’s issues scan, vulnerability assessments detect cybersecurity vulnerabilities within your network or system.
- Port Scanner: This tool checks which ports are open and active on a system so that you can close them before a hacker compromises.
- Password Cracker: Use this tool to check that the passwords you are utilizing are solid and dependable against an attack, as simple passwords can sometimes be the easiest way for a hacker to get into your system.
- Malware Scanner: A malware cloud security scanner helps find malicious codes within a system so they can be removed from files present on your PC, laptop, or server before reaching other files. Here are some great open-source malware scanners we love.
- Social Engineering Toolkit: Since this technique has become popular among hackers, using this network security toolkit is crucial in ensuring your company and workers are prepared for any cloud security breaches. This toolkit contains an SMBTrap, which can be used for sending spoofed emails and phishing attacks; an SE Toolkit, which can be used for carrying out different types of social engineering attacks; an SETunnel, which is used for formulating phishing attacks by creating a reverse connection back to the hacker's machine; and a Send-Email tool that is used to send phishing emails.
- Network Mapping Tools: These are network discovery tools such as nmap that can be used to find all your internal resources like files, servers, and printers within your system without having any prior knowledge of their IPs or names. These tools then index this information so that auditors know about all the resources available on your system.
IT Security Audits FAQs
What is an IT Security Audit, and How is it Performed?
What is included in an IT security audit?
An IT security audit includes reports on potential data and network security issues, provides an understanding of policies and procedures within a company, suggests privacy-enhancing technology that can be used in practical cybersecurity projects finds cybersecurity vulnerabilities in the existing IT security system and advises on the best way to address such data and network security issues.
What documents are required for an IT security audit? What is a security audit checklist? How is the security audit performed?
You should collect any information regarding the current state of data and network security, malware protection, mitigation techniques, and any other security procedures the company uses to prevent cloud security breaches. This will give auditors somewhere to store solutions to any data and network security issues discovered. Auditors look at what is currently being utilized for protection purposes and then scan for cybersecurity vulnerabilities within such prevention services.
How do I become an IT security auditor?
Most often, an IT security auditor must have a Bachelor’s degree. This needs to be within cybersecurity, computer science, or information technology. You would also need a handful of years of experience within the IT and cybersecurity world before having the opportunity to become an IT security auditor.
Final Thoughts on the Importance of IT Security Audits
IT security audits are growing in popularity as cyberattacks, cloud security breaches, data and network security issues, and other threats constantly put companies at risk. Conduct a comprehensive audit that will identify cybersecurity vulnerabilities within your organization's systems so they can be addressed before an attack occurs.





















