Anatomy of a Linux Ransomware Attack

Ransomware has dominated cybersecurity news headlines for the past decade, and for good reason. Through a combination of advanced encryption and effective extortion mechanisms, a ransomware attack can have devastating consequences for any victim including data loss, reputation harm, recovery costs and significant downtime.
While 85% of ransomware attacks target Windows systems, Linux is becoming an increasingly popular target due to the high value of the devices it powers - namely, servers that administer enterprise and government networks, web services and massive databases owned by organizations that can afford to pay to have operations and critical data restored after an attack. Although ransomware variants that target Linux devices are still in the minority, Linux ransomware has proven to be diverse and sophisticated in its distribution techniques and extortion methods. In this article, we’ll examine the anatomy of a Linux ransomware attack, explore the magnitude of the ransomware risk Linux users face compared to Windows users and offer some tips and advice for protecting against Linux ransomware.
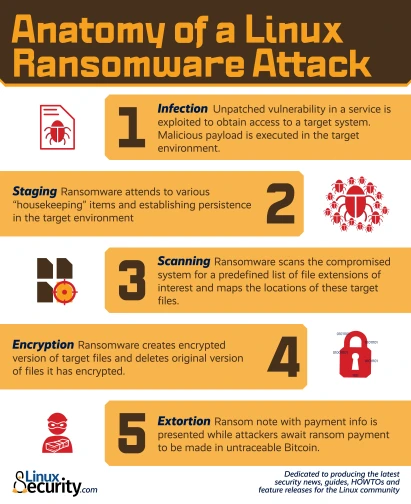
Anatomy of a Linux Ransomware Attack
Linux ransomware can be characterized by the sophistication and diversity of the tactics, methods and techniques that it employs to compromise systems and generate profits for its operators. Ransomware attacks targeting Linux systems are generally carried out in a series of clearly-defined steps, beginning with the exploitation of one or multiple unpatched vulnerabilities and ending with a payday for the attackers. Let’s take a closer look at the anatomy of a Linux ransomware attack, broken down step-by-step, to help you gain a more thorough understanding of this growing threat to your systems and your data.
Step 1: Infection
Unlike Windows ransomware variants which spread via email or maladvertising, Linux ransomware infection relies on vulnerability exploitation. Linux ransomware exploits either unpatched system vulnerabilities or flaws in a service, such as a web server or email server, to obtain access to a target system and compromise files. For instance, the infamous Lilocked ransomware exploits out-of-date versions of the Exim message transfer agent to gain a foothold in a target environment. Rex, another dangerous strain of Linux ransomware, uses vulnerability scanners specific to Drupal, WordPress, Magento, Kerner, Airos, Exagrid, and Jetspeed to detect SQL injection vulnerabilities that can be exploited to gain admin credentials.
Once in the target environment, the ransomware operator “phones home” to download a hidden executable by connecting to a predefined list of IP addresses that host the command-and-control (C2) server. At this point, the attacker typically copies the malicious executable to a local directory such as the Temp folder and then terminates and removes the script. The malicious payload is now executed in the target environment.
Linux ransomware strains often possess privilege escalation capabilities, such as those seen in the notorious Lucifer and NotPetya variants. These advanced features enable ransomware operators to access parts of a system that would be inaccessible without privileged access. While Linux ransomware typically only affects those using the web server that is compromised, privilege escalation can magnify both the scope of an attack and its overall impact.
Step 2: Staging
This step can be seen as the “housekeeping” portion of a Linux ransomware attack. The ransomware sets itself up for smooth operation by attending to various items including moving itself to a new folder and establishing persistence in the target environment, giving it capabilities such as the ability to run at boot, to run when in recovery mode and to disable recovery mode altogether. At this stage of the attack, the ransomware communicates with the C2 server to negotiate its public key, which the operator generates and places in the ransomware to encrypt the randomly-generated symmetric key.
Step 3: Scanning
Now that the ransomware has established persistence and set itself up for success, it prepares to encrypt target files. The ransomware scans compromised systems for a predefined list of file extensions and cloud file storage repositories of interest, mapping the locations of these files and repositories.
Step 4: Encryption
The encryption phase of an attack is when the real damage is done. Up until this point, nothing potentially irreversible has happened - the malware has simply set itself up and surveyed the target environment. Now, the ransomware creates an encrypted version of the target files using a random symmetric key it generates and encrypts the symmetric key with its public key. It then deletes the original version of the files it has encrypted. For every location where files have been encrypted, copies of auto-generated ransom notes are created in multiple formats.
In the event that either network storage or cloud storage locations that were discovered and mapped in the scanning process become unavailable, ransomware can patiently lay dormant in the target environment (relying on the persistence it established during the staging phase) until these locations become available for encryption once again.
Step 5: Extortion
Once the encryption process is complete, a ransom note providing explicit payment instructions is displayed as the victim's desktop wallpaper. At this point, the ransomware terminates and deletes itself, as its mission in the target environment is complete.
Meanwhile, ransomware operators wait for ransom to be paid in untraceable Bitcoin to a wallet they own. The victim must decide if he or she is willing to pay the ransom in exchange for the decryption of locked files, or accept the fact that the files encrypted in the attack are permanently inaccessible. It is often helpful to enlist a ransomware recovery firm at this point, as they can offer advice and, in some cases, locate a decryption key that can be used to recover locked files.
Key Takeaways
Linux ransomware is on the rise, but ransomware risk is still significantly lower for Linux users than for their Windows- and MacOS-using counterparts. Although Linux is becoming an increasingly attractive target among ransomware developers and operators, the vast majority of ransomware still targets Windows systems, and as a result of the privilege system that Linux adheres to, the impact of a ransomware attack exploiting a vulnerable Linux web server is generally much smaller than a ransomware attack affecting a Windows system.
In addition, because Linux is an open-source OS, Linux source code undergoes constant scrutiny from the “many eyes” of the global open-source community. As a result, vulnerabilities in Linux that could potentially be exploited in ransomware attacks are generally identified and fixed much faster than security bugs that exist in proprietary OSes.
That being said, Linux ransomware is a serious and growing threat that all administrators and users face - and must be viewed as such. Because Linux ransomware attacks exploit unpatched vulnerabilities, responsible, secure administration is critical in preventing compromise. LinuxSecurity Founder Dave Wreski explains,”The majority of attacks on Linux servers can be attributed to misconfigurations and poor administration. Frequently testing and verifying server security is the only way administrators can ensure that their servers are safe from ransomware, rootkits and other malicious exploits.”
Here are our top tips and advice for protecting against Linux ransomware:
- Backup critical files and diversify the storage media to avoid a single point of failure (SPOF). This won’t prevent an attack, but can mitigate potential damage.
- Keep servers and endpoints up to date to ensure that they use the latest security patches.
- Implement the principle of least privilege for user accounts.
- Monitor network activity and system logs closely.
- Keep tabs on event logs to identify anomalous behavior before it causes harm.
- Use a combination of IP filtering, an intrusion detection system (IDS) and an intrusion prevention system (IPS).
- Use Linux security extensions that control and restrict access to data or network resources.
- Implement robust network segmentation and data compartmentalization to minimize the impact of a potential ransomware attack.
- Audit systems regularly.
The Bottom Line: Linux ransomware is a serious and increasingly prevalent threat; however, attacks can be prevented with sound administration and the implementation of security best practices.