BlackHat USA 2022: Devils Are in the File Descriptors

Learn about a File Descriptor vulnerability that was exposed at Blackhat USA 2022, and the lessons we can take away from this discovery.
Brief Overview of File Descriptor Vulnerability that was Exposed at Blackhat USA 2022
“File descriptor or fd is widely used in the Linux kernel. Exporting an fd to user space and importing an fd from user space are very common and basic operations in the Linux kernel. However, we discovered that there are many types of high-risk vulnerabilities lurking in the usage of these operations. We discovered that the usage of fd importing operations in the Linux kernel can be a very vulnerable scenario. Several new types of vulnerabilities were found in the scenario and will be revealed for the first time. We also found that known types of vulnerabilities like type confusion are still widespread in the scenario unexpectedly. Moreover, we found a dozen vulnerabilities in the usage of fd exporting operations in kernels. These vulnerabilities exist in the Linux and Android kernels, affecting millions of devices. A comprehensive overview of vulnerabilities in the usage of fd operations will be summarized and thoroughly disclosed in this presentation.”
What is a File Descriptor?
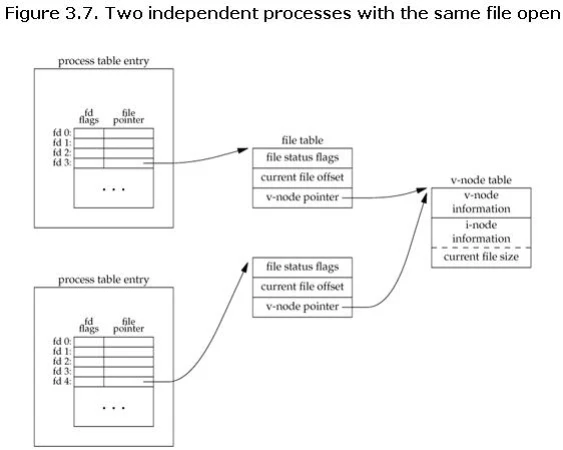
A file descriptor is a number used by the operating system of a computer to specifically identify an open file. To put it another way, when a file is opened, the operating system produces an entry to serve as a representation of the file and to hold data about the opened file. Therefore, if your OS has 100 open files, there will be 100 entries somewhere in the kernel. To the kernel, all open files are referred to by File Descriptors. A file descriptor is always a non-negative number. The kernel returns a file descriptor to the process each time we open or create a new file. A table of all active, open file descriptors is kept by the kernel. File descriptors are typically assigned in a sequential order, and the next available file descriptor from the pool is assigned to the file. When a file is closed, the file descriptor is released and made available for new allocations. Look at the image below for a better description:
Essentially, everything is stored in a “table”, or better known as an array. At Blackhat USA 2022, Le Wu showed us a quick overview of how the file descriptor process works:
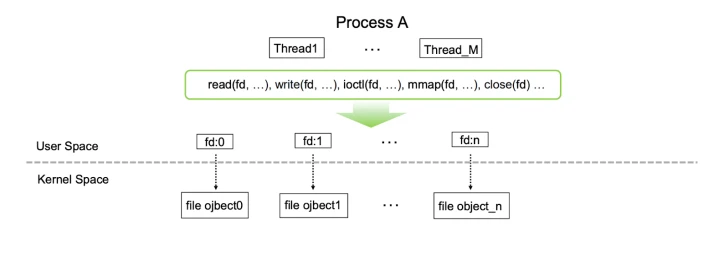
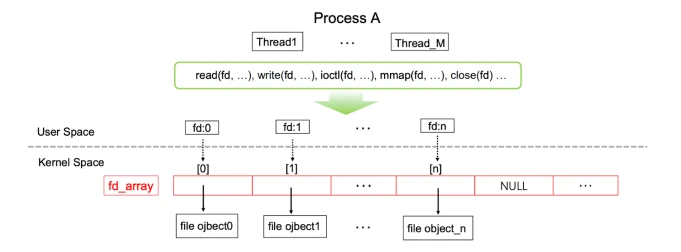
For all operations, whether it be read, write, import, export, etc, there is the array in the Kernel space and the file descriptor within the user space. We will discuss a little further how this entire process can be a vulnerability.
Known FD Vulnerabilities: Why File Descriptors?
Throughout the presentation, I constantly questioned why File Descriptors? And I was quickly given the answer: CVE-2021-0920 and CVE-2021-0929. The reason why these are so important is because they exploit vulnerabilities with File Descriptors. CVE-2021-0920 was an exploit for Linux socket syscall 0-day that allowed attackers to remotely root Samsung devices. This issue was initially discovered in 2016 by a RedHat kernel developer and disclosed in a public email thread, but the Linux kernel community did not patch the issue until it was re-reported in 2021. With CVE-2021-0929, there was a possible way to corrupt memory due to a use after free. This led to local escalation of privilege with no additional execution privileges needed and user interaction was not needed for exploitation.
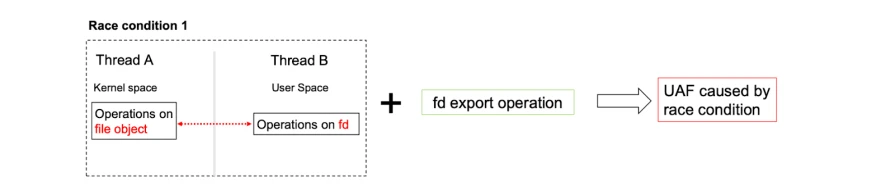
Due to a race condition in the garbage collection system for SCM_RIGHTS, CVE-2021-0920 is a use-after-free (UAF) vulnerability. Unix-domain sockets can send an open file descriptor from one process to another by using the control message SCM RIGHTS. In other words, a file descriptor is transmitted by the sender, and a file descriptor is subsequently received by the receiver from the sender. Reference-counting file structs become more complex due to this handling of file descriptors. The Linux kernel community created a unique trash collection method to take this into account. This garbage collecting system has a vulnerability identified as CVE-2021-0920. An attacker can take advantage of the UAF by succeeding in a race condition during the garbage collecting operation. Just as CVE-2021-0920, CVE-2021-0929 also shares between kernel space and user space, which called for concern since a race condition can happen between kernel and user operations. Maybe there are issues in these race conditions? During the presentation, the presenter constructed such race conditions in the fd export and import operations!
Results from Test Cases:
Case 1 – Export Operations on File Descriptors:
Case 2 – Import Operations on File Descriptors:
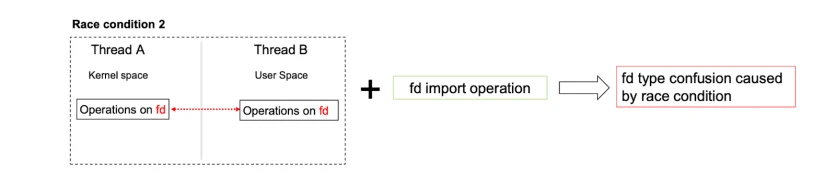
When given a special race condition, an attacker could possibly affect the import/export operation to make the device do certain actions.
What Can These Old, Patched Vulnerabilities Do?
CVE-2022-28350, which was already considered patched and highly critical, states “Arm Mali GPU Kernel Driver allows improper GPU operations in Valhall r29p0 through r36p0 before r37p0 to reach a use-after-free situation.” Although this was considered patched and fixed, Le Wu, the presenter, found a way to exploit it in two ways:
- UAF caused by race condition in fd export operation
- Fd type confusion caused by race condition in fd import operation
With this in mind, they succeed in “stealing” privileged files from others! Moreover, If the SELinux is disabled, the unprivileged process used to steal these privileged files will have the ability to read/write the “stolen” privileged file. The exploitation method of “stealing” privileged files from others has been mentioned by Mathias Krause 99 as well.
Our thoughts
When speaking about the facts of these vulnerabilities and listening throughout the presentation, firstly, we see that GPU drivers are more vulnerable. Examples of vulnerable ones include ARM mali GPU driver, AMD GPU driver, etc. Secondly, the kernel drivers which use the dma-buf interfaces are more vulnerable. Thirdly, because of the peculiarities of these vulnerabilities, some of them can hardly be found by fuzzers like syzkaller. To overcome the difficulty of finding these vulnerabilities in the usage of fd operations, and to prevent them from happening to begin with, it is important to make sure programmers use best coding practices. With the rise of API attacks and cyber criminals who constantly look for vulnerabilities like these and revisit old vulnerabilities to see what they can find, it is crucial to maintain good practice. I would like to thank Le Wu for the wonderful presentation at BlackHat USA 2022! Check US 22 Wu Devils Are in the File for the full presentation!


















