How To Encrypt Files on Linux

In our increasingly digital society, protecting the privacy of sensitive data and our behavior online is a universal concern. Many users switch to Linux for its superior privacy features and the excellent selection of privacy-focused distros that it offers.
Regardless of the OS you are using, encryption is a critical element of digital privacy. In this article, we explore the best and most reliable methods of file encryption on Linux. Our experts have firsthand experience using these programs and understand the technology behind them, equipping us with the knowledge to help you securely encrypt files on your Linux system and avoid common pitfalls associated with Linux file encryption.
What Is Encryption?
Encryption is the process of encoding data in such a way that only authorized parties will be able to read it. Encrypted data can only be decoded by a decryption key. Public-key cryptography, which uses pairs of public keys that may be known by others and private keys that may never be known by anyone except for the owner, is the basis for all encryption today. This system enables anybody to encrypt a message using the intended receiver's public key. The encrypted message can then only be decrypted with the receiver's private key. Public key algorithms underpin numerous modern Internet standards and protocols including TLS, S/MIME, PGP and GPG.
Proper Encryption & Decryption Key Management & Storage
As you can now see, proper, secure encryption and decryption key management and storage is critical in ensuring that encrypted files remain secure and accessible to authorized parties, while remaining inaccessible to unauthorized parties. If an encryption key is lost or stolen, data that has been encrypted with this key can never be recovered- and could potentially end up in the hands of cyber thieves. Thus, encryption keys should always be backed up and stored offline in a secure location, such as in a USB key kept in your safety deposit box.
Our Top Linux File Encryption Methods
There are numerous excellent methods and programs that can be used to encrypt files on Linux, so selecting the best one for your specific needs may seem a bit overwhelming. To help you make an informed decision, we’ll introduce you to some of our favorites.
Archive Manager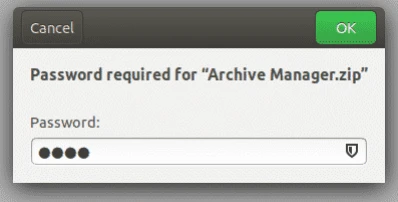
A general Archive Manager is preinstalled in all Linux systems, and is the most basic way to encrypt files o
n Linux. Encrypting files using the the Archive Manager is quite simple:
- Right-click on the file you want to encrypt and then click on “Compress”.
- Select the .zip extension and then click on “Create”.
- Open the zip file you’ve created and click on the hamburger icon at the top right of the file.
- Select the password option from the drop-down
menu and set up your password. - Click on “Save”. Your files are now encrypted with a password.
GnuPG
GnuPG (aka GPG or Gnu Privacy Guard), which is pre-installed in most distros, allows users to encrypt files and sign them using the Command Line. This unique hybrid encryption tool employs a two-prong approach to encryption to help speed up the encryption process without compromising security. This involves using both conventional symmetric-key cryptography, as well as public-key cryptography.
GnuPG comes with a collection of frontend applications and libraries, and features a versatile key management system along with access modules for a wide range of public key directories. You can download GnuPG index.
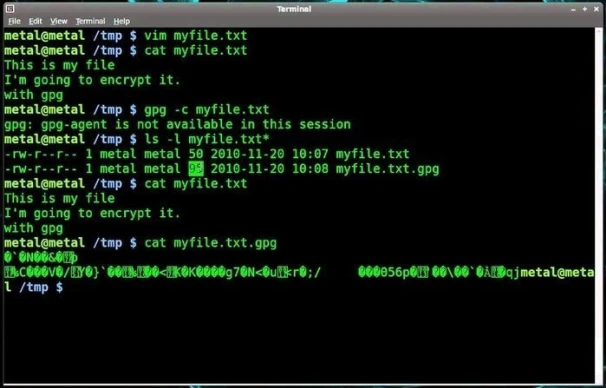
Source: Ubuntu Pit
You can learn how to encrypt and decrypt files with GnuPG on Linux in this How-To Geek tutorial.
Nautilus
Nautilus is a great alternative for users who are more comfortable using a GUI than the Command Line. The software, which encrypts files with either a passphrase or a key, can be used for the encryption and decryption of data, and also functions as a file manager.
To install Nautilus on your Debian system, run the following command:
$ sudo apt-get install seahorse-nautilus -y
Once installed, restart Nautilus with the following command:
$ nautilus -q
To encrypt files using Nautilus:
- Go to the folder where the file that you want to encrypt resides. Right-click on the file and then click on “Encrypt”.
- Now you have two options: Either select a paraphrase that will prompt you to enter a password to encrypt your file or choose a key that you have already created beforehand to encrypt your file.
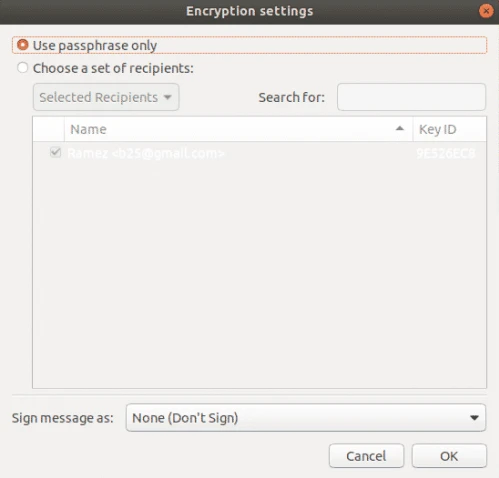
To decrypt a file:
- Right-click on the encrypted file and then click on “Open With Decrypt File”.
- Enter your passphrase.
TOMB
Tomb is a simple, user-friendly Command Line encryption tool popular among Linux user-developers. A defining feature of Tomb is its ability to generate password-protected encrypted storage vaults referred to as “tombs”. These tombs can be safely transported and hidden in a filesystem, and can be separated for additional security. For instance, your tomb file can be kept on your hard disk and the key files in a USB stick. Unfortunately, Tomb does not have a graphical user interface (GUI) and relies on Command Line input in order to function.
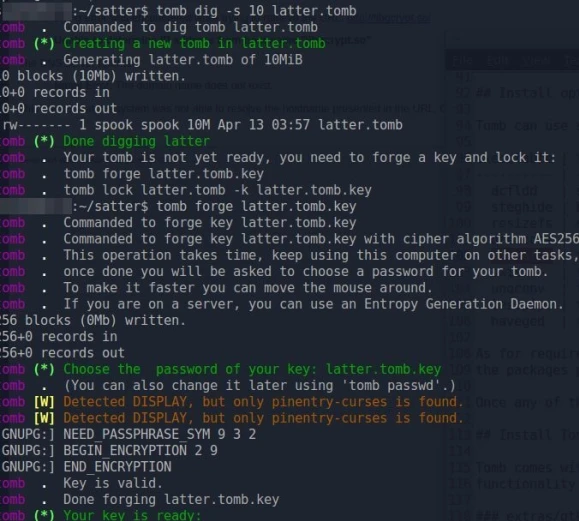
You can install Tomb from the project’s Github page.
Learn how to create tombs and how to hide a tomb key in an image in this Tecmint tutorial.
CryFS
CryFS is an excellent cloud-based tool that lets you encrypt your files and store them anywhere. It is compatible with popular cloud services like Dropbox, iCloud and OneDrive, among many others. CryFS works in the background, so you won’t notice it when accessing your files. The tool goes way beyond just encrypting your files- it also encrypts your file sizes, metadata and directory structure.
The base directory contains a configuration file that is encrypted twice - once with aes-256-gcm and once with a password that you choose. This password is also used to conduct integrity checks.
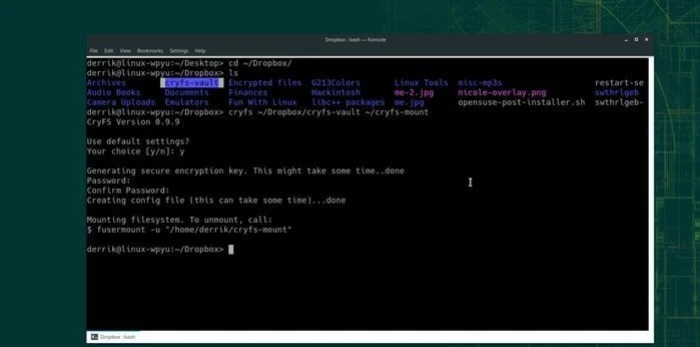
You can download the latest version of CryFS, CryFS 0.10.2, CryFS Downloads.
Learn how to use CryFS in this tutorial.
7-zip
7-zip offers strong, straightforward Command Line encryption using 256-AES encryption, along with a very high compression ratio. The official name of 7-zip for Linux is p7zip. The "p" here is short for POSIX (an open standard designed to make applications compatible across different platforms), to indicate that p7zip is a POSIX compliant implementation of 7-zip. 7-zip is also a powerful file manager. You can download the latest version of 7-zip, 7-zip 21.01 alpha, 7-zip downloads.
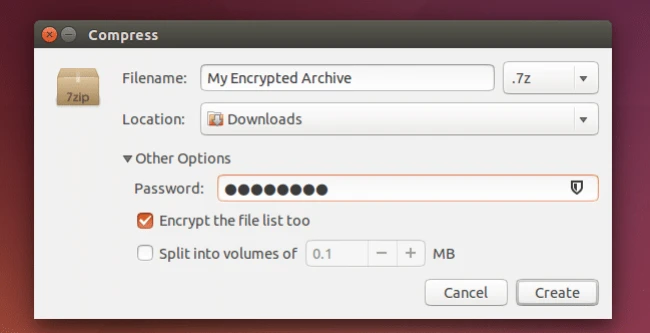
Learn how to encrypt files on Linux using 7-zip in this TechRepublic tutorial.
Tails OS
Tails is a specialized secure Linux distro created for a privacy-oriented user experience. The OS is referred to as the ‘amnesic incognito live system’, as it can only be accessed through an external USB drive on a amnesic host computer, meaning that it will have nothing but the new default form on every single usage. All Tails connections run through the Tor network - concealing users’ location and other private information.
Tails features a selection of built-in state-of-the-art cryptography and security measures including:
- Encryption and signing of emails by default using OpenPGP whenever you use the email client, text editor, or the file browser
- Instant messages are protected with robust encryption using Off-The-Record messaging (OTR)
- Files are securely deleted (with no option of recovery) using Nautilus Wipe
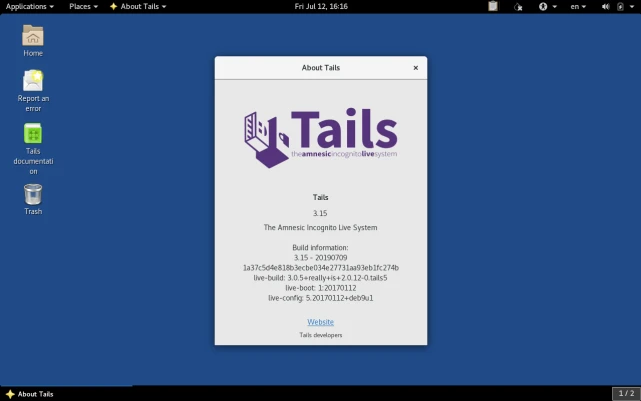
You can download Tails OS on your Linux system Tails OS Downloads.
Learn more about Tails OS and why it is among our favorite secure Linux distros in this LinuxSecurity feature article.
Conclusion
With cyberattacks and privacy issues becoming an increasingly serious and prevalent threat, users must secure data using strong encryption. Luckily, Linux offers a selection of highly secure and reliable file encryption methods, many of which you are now familiar with.
Are you using any of the methods introduced in this article, or other Linux file encryption methods we didn’t explore? Let’s discuss! Connect with us on social media:



















