WordPress Security Vulnerabilities: FAQs and Solutions

As businesses continue to require a website for promoting content online, the demand for easy-to-navigate management systems remains necessary. Fortunately, WordPress is a platform that gives inexperienced, non-technical users a chance to create professional websites that can bring in traffic and attention. W3Techs explained that forty-three percent of companies utilized WordPress for their websites in 2022.
While it is fantastic that WordPress has allowed so many organizations to establish themselves online, WordPress’ widespread use has turned it into a target for malicious hackers, who can install malware, phishing attacks, and other network security issues on a server. Threat actors use WordPress security vulnerabilities to effectively hack into systems to steal valuable data and maintain their presence through harmful software.
Organizations must learn how to secure their WordPress server against damaging data and network security threats that could result in cloud security breaches and data loss. This article will answer a few WordPress FAQs, explain how you can improve your security posture on WordPress, and demonstrate how one solution works to mitigate an attack.
Is WordPress Secure? And Other FAQs
WordPress is an online content management system where you can set up a website, forum, mailing list, membership site, and online storefronts. The server offers users default encryption methods, firewalls, frequent monitoring, and backup and recovery. Their website also suggests a few best practices that website owners implement to strengthen data and network security. The built-in features of WordPress make the domain a secure, immediate solution for users. However, network security threats can bypass security measures to harm a company on WordPress.
Why Is WordPress A Popular Target Among Malicious Hackers?
WordPress is a favorite target for cyber thieves due to its popularity on the Internet. As more companies use the platform for their online domains, hackers develop more opportunities to implement against WordPress exploits in cybersecurity.
What Common Security Issues Does It Have?
Threat actors can target multiple websites simultaneously due to the similar setups on WordPress. Cybercriminals can efficiently launch malicious phishing campaigns on WordPress through repeated brute-force attacks, Cross-Site Scripting (XSS), Denial of Service (DoS), and malware. Employees must also know the best practices for organizing their online platform. Frequent misconfigurations, predictable login information, outdated plugins, and CMS versions can give malicious actors easy ways to hack a system and install harmful software on a server.
Why Does WordPress Security Matter?
If WordPress environments face attacks in network security, one website can impact thousands of others. While the other servers were not compromised initially, WordPress security vulnerabilities across platforms can result in severe, widespread consequences for employees, companies, and clients. Sensitive data compromise, malicious software, and ransomware can cause lasting reputational harm, significant downtime, and financial loss for a business.
Vali Cyber Vice President of Product and Technical Marketing Drew Vanover explains, “Shared cloud computing offers many benefits to customers, such as not needing to maintain hardware or patching in cybersecurity on operating systems. However, this shared model also shares the increased risks of a successful attack.” He elaborates, “It is not just the hosting provider's customers that are impacted, but the hosting provider itself has to deal with the repercussions, remediation, brand exposure, and customer reactions in the wake of a successful attack. Because it is a shared environment, the odds are in the malicious actor's favor; it only takes one vulnerable installation to let them in.”
Organizations must do everything they can to improve the security posture for their business and ensure that their data is safe from most – if not all – network security issues that head your way.
How Can I Improve WordPress Security?
WordPress is not an unsafe platform for establishing websites, but there are a variety of cybersecurity vulnerabilities on the system that can permit hackers into a server. Fortunately, solutions like Vali Cyber ZeroLockTM can add a strong data layer and network security protection for WordPress sites. Defend against malicious attacks in network security to maintain your organization's sensitive data, critical systems, and hard-earned reputation.
What is Vali Cyber ZeroLockTM?
Vali Cyber ZeroLockTM provides some of the most robust protection options for WordPress websites and Linux-based systems. ZeroLock delivers comprehensive data and network security on-premise, on the cloud, and through IoT and edge devices. The service is easy to install and manage, giving employees full access to security monitoring with Multi-Factor Authentication, ransomware, crypto-jacking protection, automated remediations, and more. According to Forrester, this purpose-built solution for securing WordPress has a remarkably low overhead of less than five percent for businesses now spending thirty-three million dollars on the cloud annually. ZeroLock is a much more cost-efficient solution for security patching than other legacy network security toolkits that can have twenty to thirty-five percent overhead costs.
Vali Cyber CTO Austin Gadient mentions, “With automated lockdown configuration and sophisticated access control capabilities combined with advanced behavioral threat detection technology, admins using ZeroLock can quickly and easily secure all of their Linux workloads against damaging attacks and detect and recover any threats that get through with minimal consumption of critical computing and human resources. Running entirely in user space, ZeroLock does not require any kernel modules and is compatible with all Linux systems kernel version 3.5 or greater and across deployment environments."
How Can ZeroLock Protect a Vulnerable WordPress Website?
A cryptominer can bypass security and remain undetected if security professionals, companies, and employees need to monitor their servers properly. As a result, hackers can exploit WordPress security vulnerabilities. Our security team demonstrates how ZeroLock combats network security issues like malware attacks before an organization loses resources, data, and time.
Phase 1: Malicious Plugin Upload
Malicious actors attempt to gain access to the targeted website using a wp-login.php console page. In this instance, the user has a weak password that the hacker figured out during a brute-force attack.
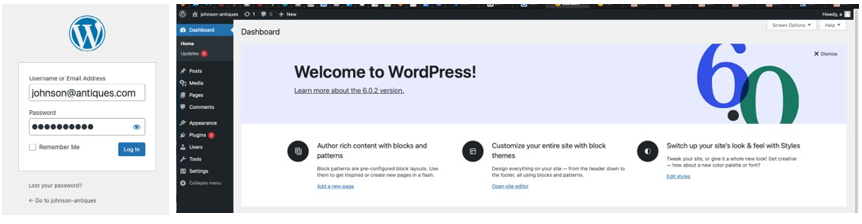
Figure 1: Attacker Brute Forces wp-login Password
With access to the target website, the attacker tries to use “Wordpress-webshell-plugin” to run arbitrary commands on WordPress through the operating system.
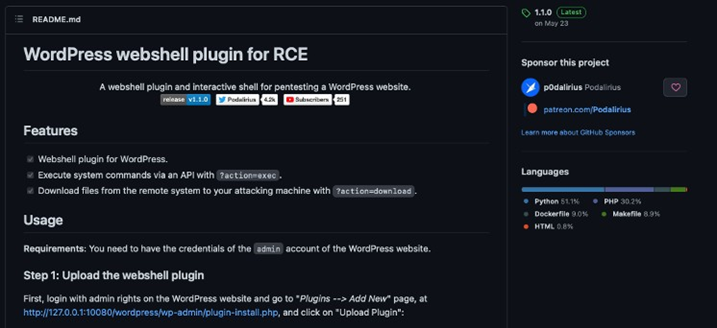
Figure 2: WordPress Webshell Plugin Github
This attempt fails since ZeroLock protects the server immediately after detecting the attack.

Figure 3: ZeroLock Alert for Malicious WordPress Plugin Upload Github
ZeroLock deletes the potential malicious PHP files the hacker uploaded so that WordPress plugins and servers remain unharmed.
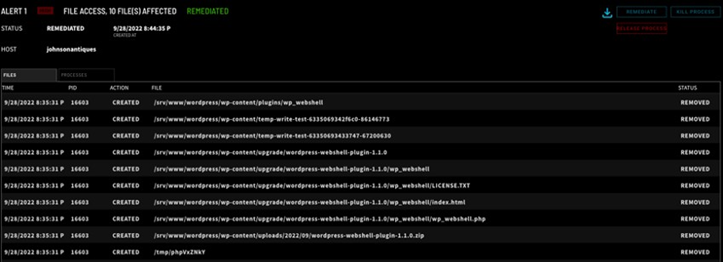
Figure 4: Files Removed by Malicious Plugin Upload Detection
Phase 2: Webshell Interaction
For this part of the demonstration, we disabled ZeroLock's plugin protection so you can see what ZeroLock can do if the above efforts succeed. The attacker plans to start a webshell by utilizing WordPress-webshell- plugin's console.py tool to run commands. console.py establishes a network connection to the WordPress-webshell-plugin, and the hacker can work on the target system.
Thankfully, ZeroLock detects webshells, too! ZeroLock receives an alert, and the “INFO” column mentions the MITRE technique T1059.
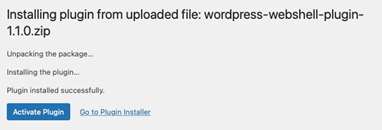
Figure 5: WordPress Plugin is Successfully Uploaded
![]()
Figure 5: console.py Webshell
ZeroLock contains detection capabilities for numerous techniques within the MITRE framework.

Figure 6: MITRE T1059 Webshell Detection
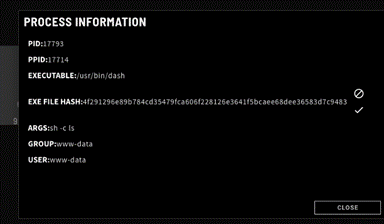
ZeroLock provides a detailed log with all indicators of compromise you could face when alerted to an attack. You can view a process tree to see all of the programs and tactics hackers use when manipulating exploits in cybersecurity. The figure below shows how Apache launched the program Dash to attempt to run the "ls".F command.
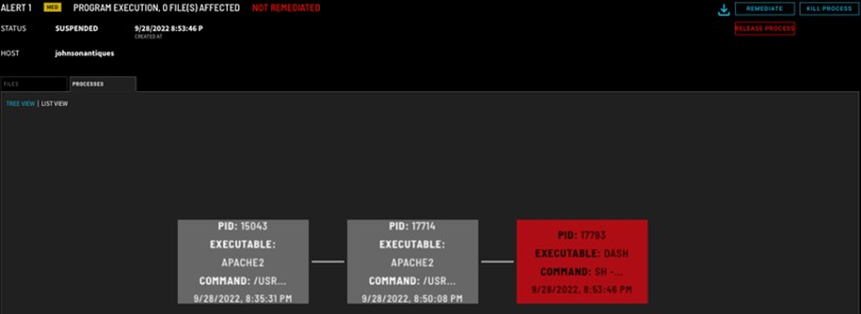
Figure 7: Webshell Process Tree
Phase 3: Malware Payloads
If the attacker could utilize the web shell (since we disabled ZeroLock's protection for this demonstration), they would have to launch the cloud security breach as an unprivileged www-data user.
Figure 8: Attempt to Run ‘ls’ Command
Figure 9: Webshell whoami Command
In this case, the threat actor chooses a crypto-jacking attack, XMRig crypto miner, since you do not need privileged access to gain cryptocurrency abilities.
Before the attack can succeed, ZeroLock uses AI to inspect the instructions the attacker executes, allowing the cybersecurity platforms to determine that a hacker is attempting an attack. Implementing AI in this process will enable ZeroLock to learn existing malware strains and immediately combat new and developing crypto mining attacks, keeping your server safe.
![]()
Figure 10: Attacker Downloads and Runs Cryptominer

Figure 11: ZeroLock’s Cryptomining Alert
Unable to use the system for crypto mining, the attacker launches a ransomware attack that would disable the website with malware Defray777 until the victims pay a ransom.
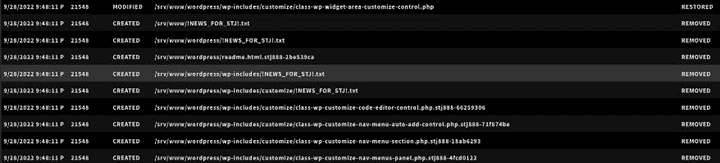
Figure 12: Attempt to Download and Execute Defray777 Ransomware
ZeroLock’s unique behavioral detection engine identifies the ransomware attack within milliseconds, and automatic remediation kicks in to clean and restore the system to its normal state.

Figure 13: Ransomware Alert
ZeroLock displays the list of any files the ransomware impacted. As a result of ZeroLock’s patent-pending rollback capabilities for Linux, the threat detection service restores encrypted files to their original state, cleans up ransom notes, and ensures that persistent ransomware does not penetrate systems. Then the website can return to its optimum operational status.
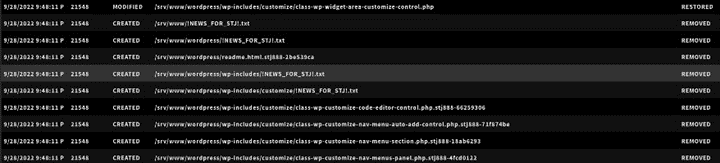
Figure 14: Files Restored by ZeroLock
LinuxSecurity expert and LinuxSecurity.com Founder Dave Wreski states, “As you can see, this is a powerful tool for detecting and remediating attacks exploiting WordPress vulnerabilities, as well as any threat to a Linux environment. With its AI and behavioral detection capabilities that identify and remediate all threats virtually instantaneously, an adversary doesn’t stand a chance of evading this solution.”
ZeroLock is a handy cybersecurity toolkit that can protect WordPress security vulnerabilities that Linux patches may have yet to take care of.
Final Thoughts on ZeroLock and WordPress Security
WordPress security vulnerabilities can leave many companies susceptible to attacks, but proper website protection can help anyone's platform stay safe. With comprehensive cybersecurity platforms like Vali Cyber ZeroLockTM, your business can implement predictive analysis detection and automated remediation to identify and remediate data and network security issues without sacrificing more time and money than necessary.
Wreski concludes, “I am thoroughly impressed with ZeroLock’s complete, minimum impact protection for WordPress websites. It’s the only threat management platform that effectively uses predictive analysis detection to stop attacks exploiting WordPress vulnerabilities that evade traditional security solutions.”
Interested in learning more? Visit valicyber.com to see if ZeroLock is the right solution for you.