Secure Docker Containers with These Data Management Software Options

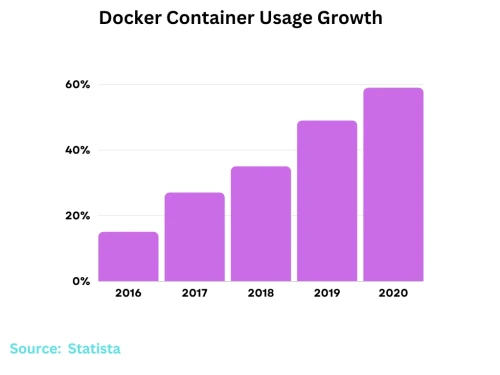
Docker containers provide a convenient way to deploy data management software. However, securing Docker containers that run sensitive data workloads requires careful configuration. Docker's lightweight container technology has become popular in current cybersecurity trends. Docker runs all applications, including databases, data pipelines, analytics tools, and other data management software. According to Docker's 2021 survey, forty-nine percent of application containers hold sensitive data. However, securing data within containers presents challenges:
- Data management software often requires access to mount points, volumes, file systems, and networks.
- Containers run with shared access to the underlying host kernel.
- Images may contain sensitive data like credentials or configuration details.
This article will discuss the Docker containers, FAQs, and other valuable details about this cybersecurity service to help reduce your chances of facing data or cloud security breaches.
What Is Docker & Why Is Image Security Important?
Docker is an open-source platform for developing, shipping, and running container applications. Containers package an application's code with all dependencies, such as libraries, binaries, and configuration files. This storage allows the application to run quickly and reliably from one computing environment to another. Docker containers share the host system's main OS kernel, but each runs in isolation. Here are a few concepts to keep in mind when securing Docker Images:
- Patch application security vulnerabilities that could lead to compromised accounts and containers by having Images create a runtime foundation for containers.
- Prevent cybercriminals from finding exploits in cybersecurity by building base Images and sharing them across projects and teams.
- Isolate host systems so you can safely share host kernels and access resources.
Overall, Docker Images users must prioritize having the ultimate security on their server to keep their containers safe.
What Are the Security Advantages of Docker Containers?
Docker containers have numerous notable data and network security benefits. Here are the most valuable ones to consider:
- Lightweight and immutable infrastructure: Share the host kernel without needing separate OSes for each container, reducing the attack surfaces and limiting exploits in cybersecurity that cybercriminals can utilize to their advantage.
- Isolation between containers: Utilize kernel namespaces and control groups to limit application damage if a threat actor compromises one container.
- Application-centric security: Focus your security policies and controls on individual applications instead of the entire OS so you can scan for cybersecurity vulnerabilities.
- Principle of least privilege: Restrict root access and only grant employees resources they need and nothing more, preventing chances of harmful attacks on network security.
- An ecosystem of tools: Benefit from endless network security toolkits that assist with vulnerability management, monitoring, runtime security, secrets management, and network segmentation.
These advantages of Docker containers can make them incredibly beneficial to organizations that need a more comprehensive platform for managing their business.
What Are the Security Limitations of Docker and Data Containers?
Although Docker containers can prove effective for a business, organizations still encounter network security issu es when running data management software within a Docker. Here are the more common concerns:
es when running data management software within a Docker. Here are the more common concerns:
- Host kernels oversee everything since containers require board access to file systems and volumes, expanding the attack surface and leaving platforms susceptible to container escapes.
- Secrets management and hardcoding can pose challenges and risks when injecting data into containers during runtimes.
- Configuring network segmentation and overlay networks to make monitoring, restricting, and isolating container communications more secure can be complex.
- Running multiple data services in a container increases the risk of lateral movement if a service faces compromise.
- Compliance requirements may dictate encryption, rigorous access controls, and auditing capabilities not native to Docker.
- Employees must restrict host system calls and resources only to those who need such access.
Docker containers can have various advantages when organizations correctly configure such services. However, various network security issues can result if a business does not appropriately manage its containers.
Docker Container Security FAQs
Should I Encrypt Data Volumes Attached to Containers?
We highly recommend encrypting volumes to protect data at rest outside the container. Bolster proper access controls to keep data secure.
What's the Most Effective Way to Isolate Data Services from Each Other in Docker?
Put services into separate container networks with restricted access between each one. Limit volume-sharing between containers.
How Can I Monitor and Audit Activity on Sensitive Data Within Containers?
Tools like Sysdig Falco allow the capture of system calls and logging container activity. Integrate additional cloud security audits and alerts with an SIEM.
Do I Still Need Antivirus Software if Running Data Solutions in Docker?
Implementing antivirus software is less critical with container isolation, but see if any of your solutions provide AV scanning that detects malware.
Best Practices for Securing Data Containers
Docker containers provide inherent data and network security advantages over regular virtual machines. Docker containers have network security toolkits that allow users to utilize some of the Docker security best practices for data management. Ensuring these benefits fortifies and strengthens your company’s data-handling process.
This holistic security and data management approach positions Docker containers as a robust solution for modern software deployment and testing scenarios. By integrating the best test data management practices, developers can prevent exposing sensitive information and ensure that data and Docker network security remain consistent across different testing environments. Here are a variety of Docker container security options you can choose from when deciding on how to bolster your cloud security frameworks:
Docker Daemon Security
- Restrict daemon access to specific users via TLS mutual authentication and certificates.
- Integrate the daemon with your OS authorization framework using SELinux or AppArmor.
- Monitor daemon activity closely using tools like Falco to detect anomalous behavior and other network security issues.
Docker Image Security
- Ensure your base image packages only come from trusted sources when installing them.
- Avoid storing actual data within images and focus only on necessary configuration.
- Scan images for cybersecurity vulnerabilities using Trivy, Anchor, or similar network security toolkits during the build.
- Sign images via Docker Content Trust and enable image verification before deployment.
Container Runtime Security
- Leverage Docker security profiles to restrict container capabilities based on the principle of least privilege.
- Prevent container escape to host using namespaces, control groups, and additional SELinux/AppArmor policies.
- Employ strict resource limits on containers via control groups.
- Mask sensitive mount points like /proc to limit host access.
Secrets Management
- Pass sensitive credentials securely at runtime via network security toolkits like HashiCorp Vault, AWS Secrets Manager, etc.
- Integrate secrets management with your identity provider, like Active Directory, Okta, and Auth0.
- Rotate secrets periodically.
Network Security
- Place data services in separate container networks with firewall rules and policies restricting inter-network access.
- Disable inter-container communication between containers holding different data.
- Route outbound traffic from containers through proxies, firewalls, and VPNs. Do not allow direct Internet access.
- Integrate Docker networks with existing corporate virtual networks and network security websites or groups.
Kernel Namespaces
- Give each container its own namespace to utilize.
- Isolate processes and system resources from other containers and hosts.
Control Groups (Cgroups)
- Oversee and limit the use of container resources.
- Prevent attacks in network security by implementing container resources that prevent containers from impacting one another.
Linux Kernel Capabilities
- Grant employees specific privileges without providing full root access.
- Minimize risk by preventing more employees than necessary from having complete access to a container.
Docker Content Trust Signature Verification
- Improve security posture with image signature verification.
- Enforce security policies regarding image usage to keep your exchanges secure.
Use Namespaces
- Map root users and non-root users on the host container.
- Prevent container breakout risks to bolster data and network security.
These container security practices can guarantee higher protection for your entire server, keeping your business, employees, clients, and sensitive data safe against the newest network security threats.
Additional Best Practices to Enhance Data Security
 Lockdown and monitor data containers further with these other solutions for data and network security that you can implement on top of the practices we recommended above:
Lockdown and monitor data containers further with these other solutions for data and network security that you can implement on top of the practices we recommended above:
- Protect data at rest outside containers with whole-disk and volume encryption.
- Harden container environments with security-focused operating systems like Tails Linux.
- Detect network security threats with IDS/IPS by monitoring container network traffic.
- Improve security posture with tools that provide fine-grained controls for data.
- Integrate Docker with cybersecurity platforms that provide unified policy enforcement, network and cloud security auditing, and compliance reporting.
Final Thoughts on Securing Docker Containers
Containers running sensitive data management workloads require stringent data and network security measures and implementing Docker container security best practices to avoid exploitation. Locking down daemon access, building secure Images, hardening runtime settings, managing secrets carefully, and segmenting networks are all essential starting points for bolstering your business’s ability to fight against threats.
Linux security modules, encryption, activity monitoring, and advanced data cybersecurity platforms can further enhance protections. With vigilant security across all aspects of the container environment, companies can safely unlock the benefits of Docker for their organization.





















