Best Linux Backup Solutions to Prevent Data Loss in A Ransomware Attack

Linux ransomware is on the rise, and an attack on your system could result in the loss of critical data and significant downtime - if important files have not been backed up frequently and stored securely.
As a Linux user, you experience the best of both worlds - you can do almost anything under Linux, but you can also lose almost everything without an effective backup plan in place. This article will explore the concept of data backup, explain why implementing a successful backup strategy is critical in mitigating data loss in the event you get hit with ransomware, and introduce six backup tools we love for conveniently and securely backing up files on Linux desktops, servers and enterprise systems.
In this article, you'll learn about our six favorite Linux backup solutions, and how they compare:
Timeshift Kbackup Rsync Duplicati Amanda Bacula Top Linux Backup Tools Comparison Table
What Is Data Backup & How Can It Mitigate the Risk of Data Loss from a Ransomware Attack?
Data backup involves copying or “backing up” critical files to a secure and high-performing external system to avoid a single point of failure (SPOF). In order to prevent data loss should you experience a ransomware attack, it is extremely important to regularly backup your desktop and server, make sure that the files you create are not corrupted, and that these files are stored in a secure location such as an external hard drive or SSD. This will ensure that your backups are ready to be restored to a new or the same server in order to get your system functioning again after a ransomware attack. By using a cloud-based Linux backup tool such as the four tools we highlight in this article, admins can automate backup scheduling to ensure they don’t forget to backup critical files regularly - one of the most common challenges in implementing a successful backup strategy.
It should be noted that by implementing a proactive, defense-in depth security strategy and engaging in security best practices such as keeping servers and endpoints up-to-date, implementing the principle of least privilege for user accounts, closely monitoring network activity and system logs and auditing systems regularly, users can greatly reduce their ransomware risk - but cannot eliminate it entirely. Thus, an effective backup plan should be viewed as a critical “layer” of any successful cybersecurity strategy.
Top Tips for Secure Data Backup
Ransomware dominates security news headlines daily, and is no longer a threat to Windows users alone. While 85% of ransomware attacks still target Windows systems, Linux is becoming an increasingly popular target due to the high value of the devices it powers such as servers that administer enterprise and government networks, web services and massive databases owned by organizations that can afford to pay to have operations and critical data restored after an attack. Through a combination of advanced encryption and effective extortion mechanisms, a ransomware attack can have severe, lasting repercussions for victims including data loss, reputation harm, recovery costs and extensive downtime.
Data backup remains the best defense against data loss should you suffer a ransomware attack, and 56 percent of organizations recover their data from backups, compared to 26 percent by paying the ransom. So why are ransomware victims often unable to restore their systems from their backups? Nearly every admin and organization does backups; however, there are certain principles that must be followed in order to implement a secure, successful data backup strategy.
Data should be backed up frequently to meet recovery point objectives and keep potential data loss to an acceptable level. Recovery time objectives should be established based on an acceptable period of downtime, as restore time will often determine the true impact of a ransomware attack. We recommend using a folder comparison and synchronization software like FreeFileSync to determine the differences between a source and a target folder, so only the minimum amount of data necessary is transferred.
Because ransomware attacks typically spread across the network, including the backup environment, backups must be protected from malware in order to survive a ransomware attack. This can be accomplished with an immutable backup solution that creates snapshots which cannot be altered and maintains backups in a read-only state so they cannot be encrypted by ransomware. An “air-gapped” backup system that’s isolated from the rest of the IT environment can also protect backups from malware, but comes with cost and complexity challenges, along with the risk that scheduled backups will run before a ransomware attack is detected, and the ransomware will be backed up as well. For this reason, backups should be reviewed carefully to ensure they are not corrupted.
Diversification is also a key consideration when it comes to creating and implementing a successful data backup strategy. Admins and organizations are quickly learning the importance of defense-in-depth in any type of security. Redundancy and resilience of backups can be accomplished with a “three-two-one” backup strategy, which ensures that three copies of data are kept, with two on different media formats, one of which is off-site. This strategy makes it highly difficult for a malicious actor to encrypt and lock up every copy of their target’s data.
Finally, restoring and recovering data from backups with minimal downtime in the event of a ransomware attack is a technical and time-consuming process that should be practiced by sysadmins and IT teams regularly in order to identify and improve upon any potential weaknesses. Luckily, the cloud facilitates easy recovery testing by making data readily accessible.
Best Linux Backup Tools to Mitigate Data Loss
Timeshift (for Desktops)
Timeshift is one of the most popular tools for backing up Linux desktops that LinuxSecurity users and team members rave about. It is quick and easy to use, and comes pre-installed with many popular Linux distros, or is available in the distribution repository. Timeshift supports Btrfs, a modern copy-on-write filesystem, out of the box. Its Setup Wizard makes configuration simple and efficient, and setting up a backup configuration in Timeshift takes less than a minute. Timeshift can create system snapshots at any moment, and is a highly secure and reliable backup solution that poses no risk of data loss when backing up files.
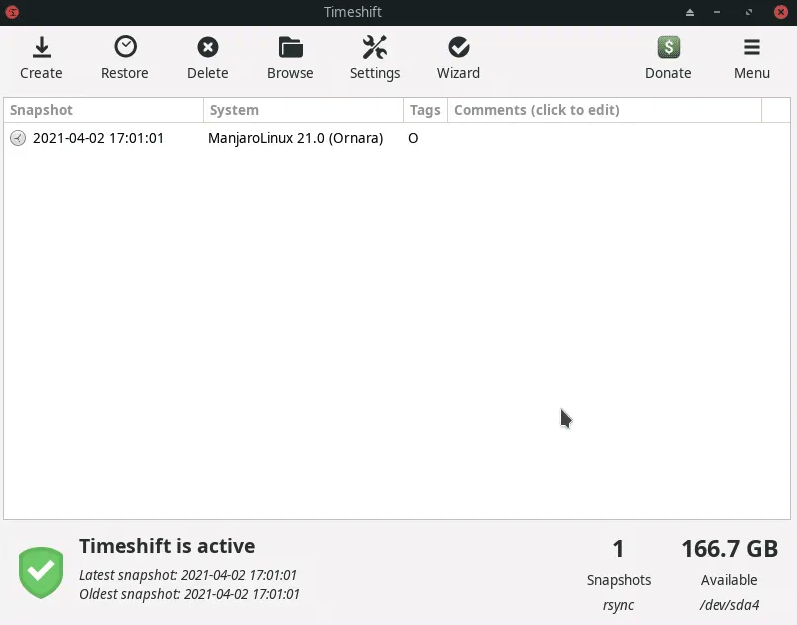
Why We Love Timeshift
- Ideal for backing up Linux desktops
- Fast and user-friendly
- Out-of-the-box Btrfs copy-on-write filesystem support enhances security and reliability
- Setup Wizard makes setup and configuration straightforward and efficient
- Can create system snapshots at any moment
- No risk of data loss when backing up files
Install Timeshift
Timeshift is available in nearly all distro repositories. Use your distro’s package manager to install Timeshift in your distribution.
To install Timeshift on an Ubuntu system, use the command:
sudo apt install timeshift
To install Timeshift on a Fedora system, use the command:
sudo dnf install timeshift
To install Timeshift on a RedHat system, use the command:
sudo yum install timeshift
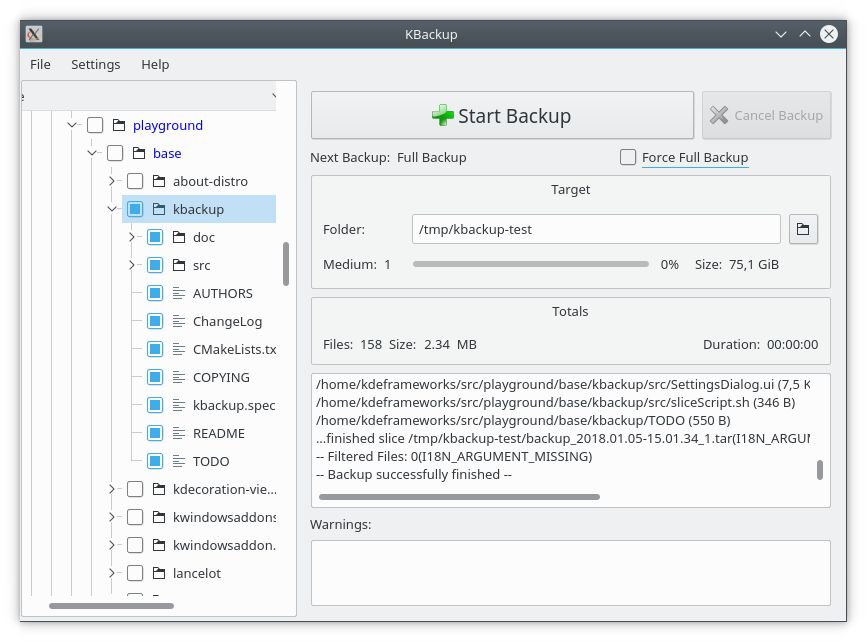
Kbackup (for Desktops)
Kbackup is a user-friendly, highly portable backup tool for both Linux and Unix that enables users to create automated, unattended backups. It creates archives and compresses them using the tar and gzip utilities, and then creates backups.
Kbackup is highly reliable and supports full or incremental backups. We love the fact that it also offers encryption and double buffering for added security, as well as support for tape drives, floppies or removable media, and remote backup across networks. Kbackup features a straightforward, menu-driven interface and Command Line interface for inclusion in automated scripts.
Install Kbackup
Run the following command to install Kbackup:
sudo apt-get install kbackup
Why We Love Kbackup
- Highly reliable, thanks to trusted and established tools like afio and tar
- Capable of creating automated, unattended backups
- Can create both full and incremental backups
- Supports tape drives, floppies or removable media, as well as remote backup across networks
- Compression, encryption and double buffering capabilities
- Features a user-friendly, menu-driven interface and Command Line interface for inclusion in automated scripts
- Highly portable due to its modular shell script design
Rsync (for Desktops & Servers)
Rsync is a simple but powerful utility that comes pre-installed with many popular Linux distros, or is available in the repository. Rsync is memory-friendly and can do anything that a file manager can do from the Command Line with a user-friendly command syntax. For instance, you can synchronize two directories by deleting existing files from the destination directory and copying all files from the backup directory using the command:
rsync -av --delete /backup/ /destination/
While rsync isn’t strictly a backup application, it’s the foundation for many of them. It’s quite possibly the most versatile file transfer application available. It was designed many years ago to synchronize two files in the most efficient way possible. It’s evolved into a robust command-line tool for maintaining files across different systems.
Rsync supports any Cloud storage destination available online, including Google Cloud and an Amazon AWS instance. You can transfer backup files to remote storage using rsync with SSH using the command:
rsync -avz backup/ user@ip_address:/home/destination/
From most modern desktops, this will automatically use SSH, but if it doesn’t, you can tunnel the file transfer through SSH using something like the following:
rsync -avze ‘ssh -i ~/.ssh/keyfile’ backup/ uiser@ip_address:/home/destination/
where “keyfile” is your ssh key, such as id_rsa or id_ed25519.
Grsync is a simple GUI for using Rsync that can be installed from your distro repository.
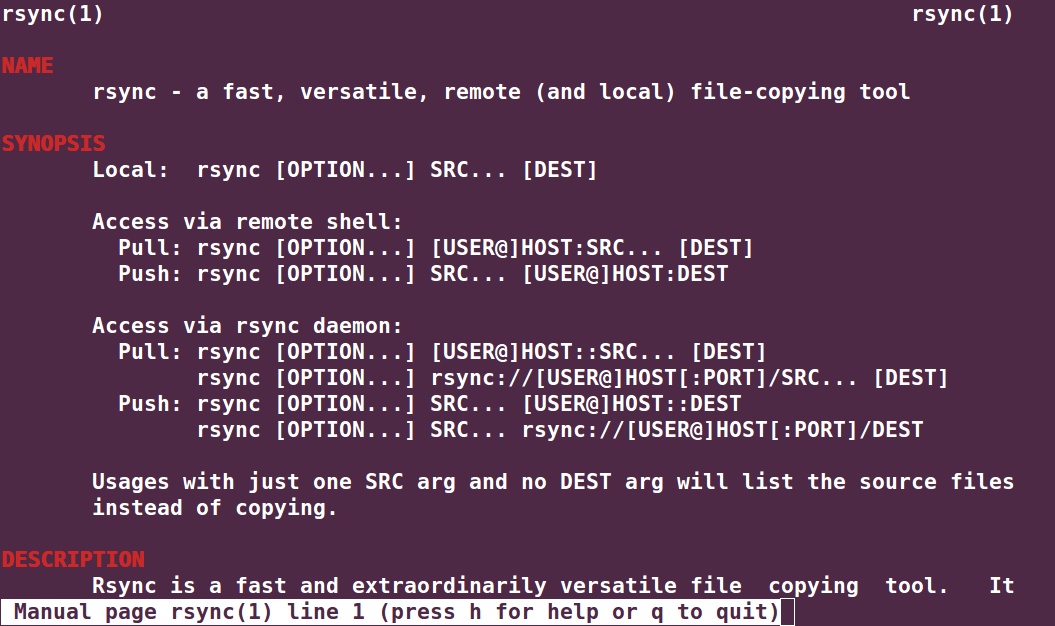
Why We Love Rsync
- Ideal for backing up both Linux desktops and servers
- Memory friendly
- Can do anything that a file manager can do from the Command Line with a user-friendly command syntax
- Supports incremental backups, making adjusting to an increased backup schedule easy
- Tunneling through SSH provides added security
- Supports both local and remote backups
- File permissions and ownership settings are preserved
- Updates both the file system and the directory tree after an operation that backs up new files on an already established backup directory structure
Duplicati (for Desktops & Servers)
Duplicati is a free and open-source backup solution that supports a wide range of popular third-party storage providers including Google Drive, Dropbox, OneDrive, Amazon S3 and Google Cloud. Duplicati also stores backups on various remote file servers using SSH, making it easy to use an off-site destination far away from the original data - a key component of securing backups against ransomware. This feature also makes it a viable solution for desktop users.
Duplicati supports incremental backups so only changed parts need to be transferred, and the tool features a built-in scheduler and auto-updater. Duplicati provides the capability to run backups on any machine through a web-based interface or via a command-line interface, or a headless machine like a NAS (network attached storage).
Duplicati uses strong AES-256 encryption to protect data privacy, and supports the use of GPG to encrypt backups as well. It also tests the content of backups regularly to detect broken backups on corrupt storage systems before it’s too late.
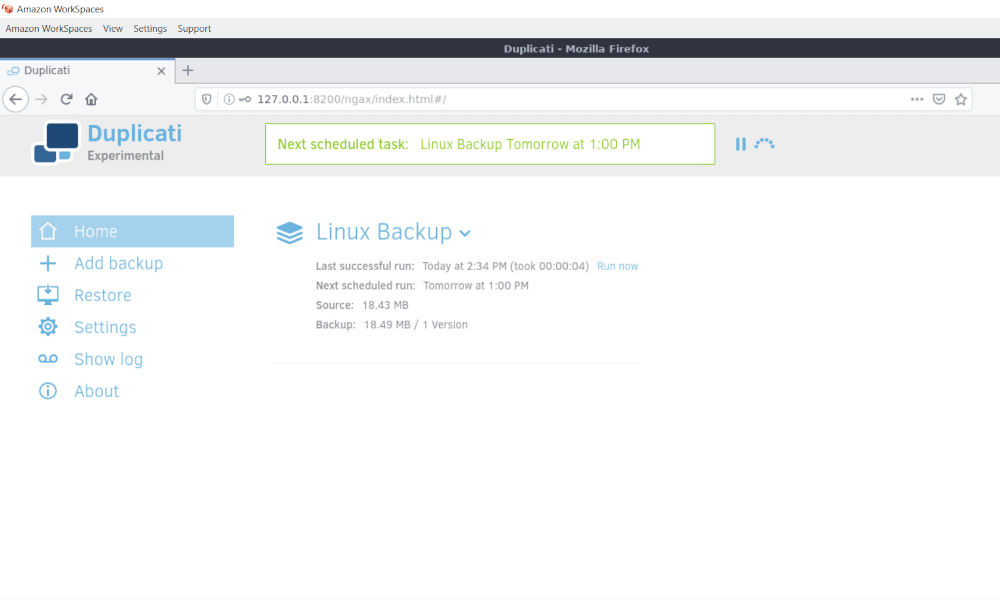
Why We Love Duplicati
- Uses AES-256 encryption (or GNU Privacy Guard) to secure all data before it is uploaded
- Uploads a full backup initially and stores smaller, incremental updates afterwards to save bandwidth and storage space
- Scheduler keeps backups up-to-date automatically and Integrated Updater notifies you when a new release is out
- Encrypted backup files are transferred to targets like FTP, Cloudfiles, WebDAV, SSH (SFTP), Amazon S3 and others, as well as various remote file servers, making it easy to use an off-site destination far away from the original data
- Available as an application with an easy-to-use user interface, and as a command-line tool
- Can make proper backups of opened or locked files using the Logical Volume Manager (LVM)
- Offers a selection of filters, deletion rules, transfer and bandwidth options, etc.
- Tests the content of backups regularly to detect broken backups on corrupt storage systems
Install Duplicati
Duplicati can be downloaded for free from the project’s GitHub page.
Amanda (for Enterprise Servers)
Amanda, the Advanced Maryland Automatic Network Disk Archiver, is a free and open-source backup solution that enables IT administrators to set up a single master backup server to back up a large number of servers and workstations running multiple versions of Linux or Unix to tape drives/changers, disks, or optical media.
Amanda provides a rapid installer to minimize installation time and an intelligent scheduler to automate backups. Amanda also offers database, application and broad platform protection, as well as automated data retention in the event of transmission faults. Backup fault tolerance ensures that in the case of a network interference, initiated backups will remain synced and will not compromise the entire backup.
While Amanda probably won’t be your first choice for a backup solution due to its complexity, it’s been around longer than most and for good reason.
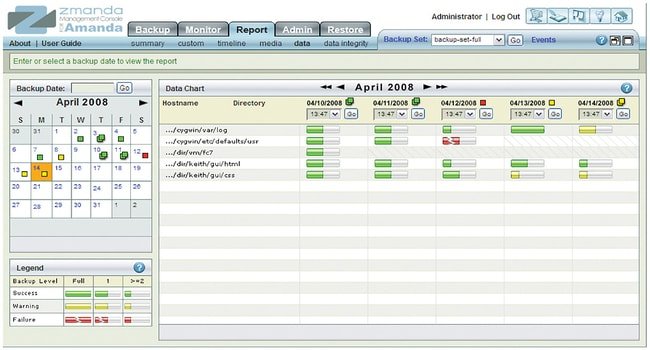
Why We Love Amanda
- Allows admins to set up a single master backup server to back up a large number of servers and workstations running multiple versions of Linux or Unix to tape drives/changers, disks, or optical media
- Rapid installer reduces installation time
- Intelligent scheduler for automating backups
- Backup fault tolerance ensures that in the case of network interference, initiated backups will remain synced and will not need to be restarted
- Application, database and broad platform protection
- Flexible media options
- Automated disposition policies
- Automated data retention in case of transmission faults
Install Amanda
Amanda binary packages can be downloaded from the project’s website. Source packages can be downloaded from the project’s SourceForge page.
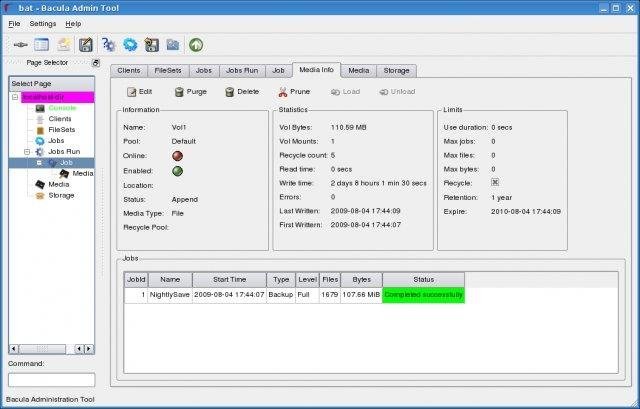
Bacula (for Enterprise Servers)
Bacula is a popular enterprise-level Linux backup solution, available in all major Linux distro repositories. LinuxSecurity admins report that it’s a bit difficult to set up, but once set up, you can easily manage its settings via a GUI or the Command Line.
Bacula can be used to create automatic backups on a remote or local server, manage backups using a CLI or a GUI, add volume pools, add storage blocks, include or exclude files, and more. Bacula uses Transport Layer Security (TLS) authentication, supports virtual backup and duplicate job control, and provides the ability to create accurate backups with compression support.
Why We Love Bacula
- Enterprise-level backup solution
- Can be used to create automatic backups on a remote or local server
- Easy to manage via a GUI or the Command Line
- Uses Transport Layer Security (TLS) authentication
- Supports virtual backup
- Duplicate job control
- Allows data compression for increased accuracy
Install Bacula
Installing Bacula using the command-line interface, begin by installing Bacula from the repositories, set up its database and edit the configuration files that exist at /etc/bacula:
/etc/bacula/bacula-dir.conf
/etc/bacula/bacula-sd.conf
/etc/bacula/bacula-fd.conf
A complete installation guide is provided that explains how to install Bacula Community binaries on Debian, Ubuntu and CentOS/RedHat.
While the set of open-source tools required to build a Bacula enterprise backup system can be downloaded for free, Bacula also offers a set of subscription-based enterprise data backup solutions that combine Snapshots, advanced deduplication, single file restores, single mailbox restores and data verification into one comprehensive platform. Bacula Enterprise also includes assistance with onboarding and implementation and customized, ongoing support.
Key Takeaways for Secure Data Backup on Linux
The threat of ransomware is here to stay, and must be proactively addressed - but also prepared for. Data backup is an essential part of secure Linux administration, and can enable you to restore your system in the event that you get hit with ransomware. Keeping on top of backups is a significant challenge for most admins, and using one of the automated, cloud-based tools introduced in this article can save time and improve the security of your system.
When choosing a Linux backup tool, admins should note functionalities like database support, the nature of the backup media, encryption support and supported data or file formats. Keep in mind that it is critical to do your research and select a reliable backup solution like one of the tools featured in this article to prevent potential compromise of sensitive information. Backup tools are a bridge connecting a server, client computer, or backup device with a data access point that is on another end, and you would not want anything to go wrong while sensitive data is passing through this bridge.
Remember, when it comes to ransomware and other cyber threats, prevention is far better than reaction. Invest in your backup strategy now. Should something ever go wrong, you’ll be very thankful you did!
Have additional questions about secure data backup on Linux? Are you using one of these tools in your backup strategy, or another tool you think we should cover? Please reach out to us on Twitter, ask questions and share your experience. We love to discuss topics like this with others who share our passion for Linux and security!
Top Linux Backup Tools Comparison Table
| Timeshift | Kbackup | Rsync | Duplicati | Amanda | Bacula | |
| For Desktops? | Yes | Yes | Yes | Yes | No | No |
| For Servers? | No | No | Yes | Yes | Yes | Yes |
| Easy to set up & configure? | Yes | Yes | Yes (for simple instances) | Yes | Yes | No |
| Full client-side encryption? | Yes | Yes | No | Yes | Yes | Yes |
| Supports file compression? | Yes | Yes | Yes | Yes | Yes | Yes |
| Creates automated backups? | Yes | Yes | Yes (with shell scripting) | Yes | Yes | Yes |
| Supports full backups? | Yes | Yes | No | Yes | Yes | Yes |
| Supports incremental backups? | Yes | Yes | Yes | Yes | Yes | Yes |
| Command-Line? | Yes | Yes | Yes | Yes | Yes | Yes |
| GUI? | Yes | Yes | Yes (Grsync) | Yes | Yes | Yes (Baculum) |
| Continuous data protection? | Yes | No | No | Yes | No | Yes |
| Best suited for: | Desktops | Desktops | Servers | Desktops & servers | Enterprise servers | Enterprise servers |
| Open-source version available? | Yes | Yes | Yes | Yes | Yes | Yes |