OctopusWAF: A Customizable Open-Source WAF for High Performance Applications

Mainstream web application firewalls (WAFs) can be very difficult to understand, with thousands of lines of code and obscure plugins. This complexity makes it challenging for developers to modify code to block specific anomalies and secure their applications. But OctopusWAF is different - the open-source WAF is customizable, user-friendly and optimized for a large number of parallel connections - making it ideal for high performance Asynchronous JavaScript and XML (AJAX) applications.
What Is a WAF?
A WAF is a piece of software or hardware intended to protect an HTTP application at the level of the application. WAFs apply a set of rules, which are designed to protect against common attacks such as Cross-site Scripting (XSS) and SQL Injection, to HTTP conversations. As proxies generally protect clients, WAFs protect servers and are deployed to protect one or many web applications. Because of this, a WAF is considered a reverse proxy.
WAFs can be customized to specific applications; however, this customization often requires significant effort, and maintenance must be performed as the application is modified.
There are two types of WAFs. The first type uses a HTTPd plugin to gather input or output data. There are multiple significant disadvantages associated with deploying this type of WAF - it is not fully portable, the developer needs to create various HTTPd plugins, and performance is often poor, to name a few.
The second type, which is an independent reverse proxy server, brings all requests made by the client to the proxy. The proxy then analyzes the content and sends all information that is not blocked to the external server.
OctopusWAF Harnesses the Power of Open Source to Maximize Performance
Cybersecurity engineer and ethical hacker Antonio Costa (known in the Hacker community as "CoolerVoid") has created OctopusWAF to maximize performance and minimize the complexity associated with deploying a WAF. OctopusWAF leverages resources from the vibrant, global open-source community, which has enabled the up-and-coming WAF to gain performance and provide lightweight, customizable web application protection. OctopusWAF is written in the C programming language and uses libevent to make multiple connections. Its event-driven architecture is optimized for a large number of parallel connections (keep-alive), making OctopusWAF ideal for high performance AJAX applications. OctopusWAF offers flexible deployment, and is the perfect WAF for endpoints that require custom protection.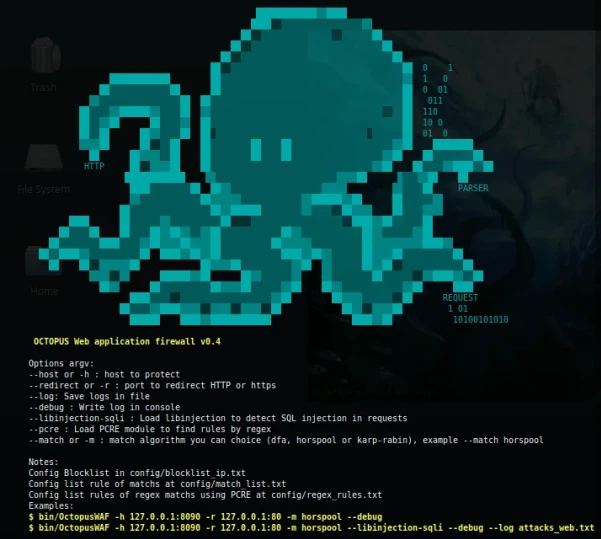
The current version of OctopusWAF, version 0.4, doesn't have the support required to load the OWASP ModSecurity CRS Project’s rules; however, developers can load custom rules in the directory "conf".
Costa encourages community involvement in the OctopusWAF project. He states, “Creating a WAF on my own has been very challenging. I am looking to grow the OctopusWAF project, and I need collaborators in order to be able to do so. Anyone that wants help is welcome to. Whether you have suggestions or code contributions - I urge you to get involved in this project. Great things are in store for the future!”
Thank you to Antonio Costa for his contributions to this article.
Additional Resources:
Watch a test libinjection in OctopusWAF: Test libinjection in OctopusWAF - YouTube
Have another open-source project that you’d like us to cover? Please let us know - we love to hear your ideas!





















