Lynis: A Linux Security Audit Tool You Should Know About

running processes, configuration files, and more to determine what areas throughout a system need fixing to improve security posture. Such tools even offer information on how to go about such adjustments.
Lynis is an open-source auditing tool that performs extensive system health scans that support system hardening and compliance testing. Lynis supports Unix-based Operating Systems (OS), like Linux, and oversees a system for general information, vulnerable software packages, and configuration issues. This tool can detect cybersecurity vulnerabilities and provide in-depth auditing for continuous improvement, unlike other auditing tools that do not offer such information.
The Lynis auditing tool assists with configuration, asset, and software patch management, as well as system hardening, pentesting, and intrusion detection. Lynis hopes to reach audiences, including system administrators, auditors, security officers, pen-testers, and security professionals, who may need help deploying hardening for web application security vulnerabilities, running daily scans for network security threats, demonstrating how to adjust security patching, and locating exploits in cybersecurity. This article will discuss Lynis installation, how to run the auditing tool and read reports, and the various testing options available through the service.
Auditing
Steps
Lynis scans systems in a modular and opportunistic way by testing found components. Scans and audits will be more extensive if Lynis finds more, though network security toolkits do not need installation for Lynis to complete a scan. The nine steps to Lynis audits are as follows:
- Initializing
- Performing basic checks
- Determining Linux Operating System and tools
- Searching for available software components
- Checking the latest Lynis version
- Running enabled plug-ins
- Testing security in each category
- Executing your custom tests (optional)
- Reporting the status of the security scan to the user
“lynis.log” will store all information once found. A separate file, “lynis-report.dat,” contains suggestions and warnings.
Installation & Running
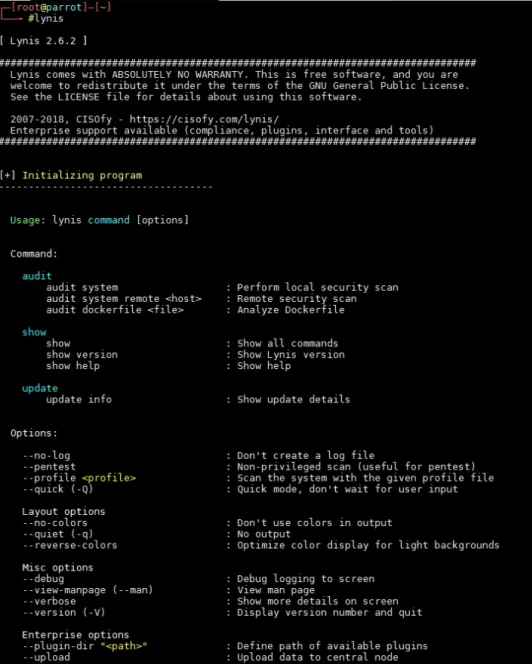
First, install Lynis and start with the following codes:
|
sudo apt-key adv --keyserver keyserver.ubuntu.com --recv-keys C80E383C3DE9F082E01391A0366C67DE91CA5D5F sudo apt install apt-transport-https echo "deb https://packages.cisofy.com/community/lynis/deb/ stable main" | sudo tee /etc/apt/sources.list.d/cisofy-lynis.list apt update apt install lynis Lynis show version |
The last code lets you know how upgraded Lynis is before using it on your system.
To code Lynis for running, perform the following codes:
|
cd lynis /lynis lynis audit system |
“/lynis” will ask you to pick an auditing option, and “lynis audit system” will execute the checks through your entire system. Here are a few other options to choose from:
|
lynis audit system remote <host> lynis audit dockerfile <file> lynis --forensics lynis --pentest |
Remote security scan Analyze docker files Forensics on running/mounted system Pentesting |
Furthermore, you can set up cronjobs to run daily scans with these codes:
|
crontab -e 30 22 * * * root /path/to/lynis -c -Q --auditor "automated" --cronjob |
This code will run scans at 10:30 P.M., outputting results to “lynis.log”
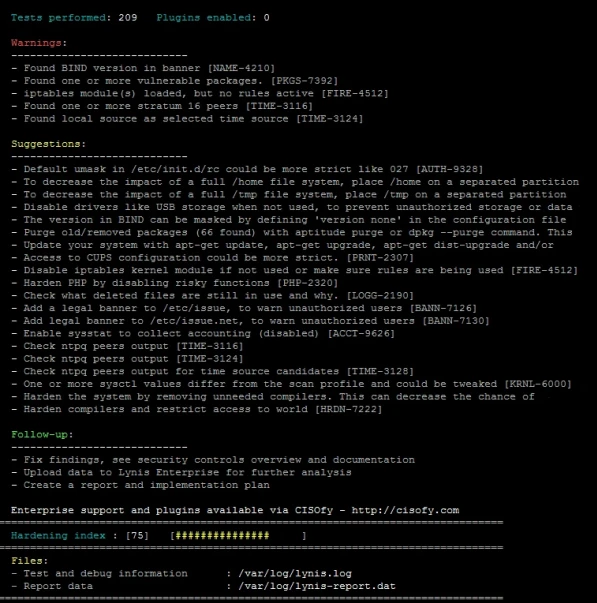
About the Reports
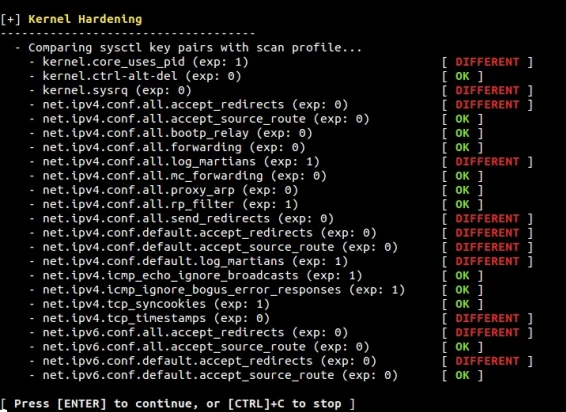
Once an audit is complete, Lynis will prevent multiple outputs:
- Result: This could state “ok” or “warning,” “found” or “not found,” and “none” or “done” based on what command you run and the outcome of that coding.
- Log File: You can see the action/event times, why a test failed or skipped, internal test outpost, configuration suggestions, and threat impact scores.
- Report File: Information and data Lynis gathers gets produced here so you can see remarks, sections, and options/values. Lynis generates details on package installations, Debian plug-in scans, and system boot and services so that you know what network security issues exist in your system.
Lynis is thorough, even presenting other test and scan results such as the following: printers and spools, software messaging and firewalls, insecure services, SSH support, SNMP support, databases, LDAP services, kernel, memory, and processes, kernel hardening, users, groups and authentication, shells, file systems, file permissions, and more.
When reading screen outputs, understand the colors, which make reading the files simpler:
- Green: Your system is exemplary, and any issues are disabled.
- Yellow: Lynis skipped a test, didn’t find a scan, or has a suggestion.
- Red: Somewhere in your system needs attention and is unsafe.
Each section can expand the color to see the network security threat and how to mitigate cybersecurity vulnerabilities. Click on the "show details" command to get suggestions to improve security posture.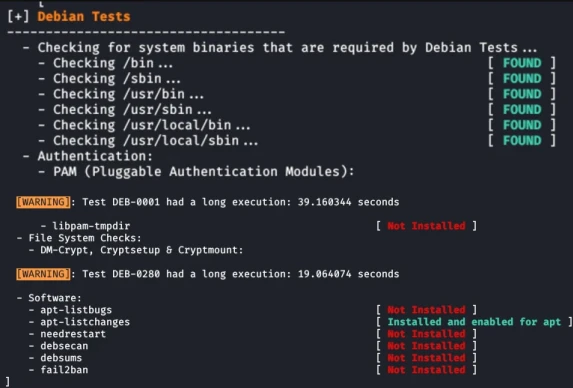
 Other Lynis Options
Other Lynis Options
Custom Tests
You can choose particular tests to run on Lynis with the command “lynis show tests.” See all the options available on your OS and their descriptions to pick the best ones for the network security issues you are scanning for. Then input these commands:
|
lynis show tests <test ID> /lynis update info /var/log/lynis.lo cat /var/log/lynis.log | grep KRNL OR ./lynis -c -Q. ./lynis –tests “<test ID> <test ID> |
These options allow you to figure out what test you want, how long it takes to run the scan, and how to set up test IDs.
Lynis with Categories
If you want to avoid using test IDs, run category tests. For example, type this for firewalls:
|
./lynis --tests-from-category “firewalls”. |
Our Final Thoughts on Lynis
Keep your system secure and up to date using these auditing network security toolkits to ensure your system is healthy. Lynis is the best option, offering comprehensive auditing and improvement suggestions. The detailed reports cover everything in the system, making it easier to know system health and what categories need your attention.
Lynis is easy to install and understand, as reports have color coding and various scanning options. Run Lynis with plug-ins and customize your scans so you stay updated on the latest cybersecurity vulnerabilities and data and network security issues.
Do you use an auditing tool to maintain the health of your systems? If not, try out Lynis! We’d love to hear your thoughts - connect with us on X @lnxsec, and let’s discuss!